What is 'Juice Jacking' and Tips to Protect Your Device From It
For most of us, our technological devices are an integral part of our lives. We use them virtually every day- for communication, entertainment, and work- without considering how secure they are. Unfortunately, consumers should be aware of a growing trend called "juice jacking" to protect themselves from possible theft or data loss due to malicious attacks. In this blog post, we'll explain what juice jacking is and provide helpful tips on keeping your device safe from this hacker technique. So let's get started!
What is Juice Jacking?
Juice jacking is a term used to describe a cyber attack technique that involves stealing sensitive data from a mobile device while charged through a public USB port. Attackers install malware or create fake charging ports to steal data from personal devices, such as smartphones and tablets, which are later used for theft, fraud, or blackmail.
Juice jacking is a growing concern, particularly in public areas with open charging stations. These stations are popular in airports, shopping malls, cafes, transportation hubs, and other public places where people frequently need to charge their mobile devices.
The attacker's modus operandi involves infiltrating free mobile charging stations with malware or tampering with it to steal data or install malware on the victim's device. When a user unknowingly plugs in their smartphone or other mobile device into a corrupted charging station, the malware is automatically downloaded into the device, which begins to steal data or install more harmful software.
Juice jacking is not only an invasion of privacy but can also result in financial losses, identity theft, and ransomware attacks. Attackers can access your bank accounts, email, social media accounts, or any other sensitive information, compromising your identity and privacy.
It is recommended that you avoid using public charging stations that are not trustworthy or use USB cables that only carry power and are not capable of transmitting data to protect your device from juice jacking. Also, it's best to always have a fully charged portable power bank to ensure you are never caught without power.
History of Juice Jacking
The history of juice jacking dates back to 2011, when a group of researchers warned that malware could be implanted into a smartphone via the USB port of a public charger. The attack can occur when a user plugs their phone into a USB port infected with malware or a fake charging station that cybercriminals have set up.
In recent years, juice jacking has become a more serious concern due to the widespread use of public charging stations at airports, cafes, and other public places. As more people rely on their mobile devices for work and personal use, they are increasingly at risk of falling victim to this attack.
In response to the growing threat of juice jacking, many security experts recommend using a personal charger or a portable power bank to avoid the risks of using public charging ports. Additionally, users should avoid using public chargers with unknown or questionable origins, as they may have been compromised with malware.
How Does Juice Jacking Work?
Juice jacking is a type of cyber attack that occurs when a hacker sets up a public charging station or USB charging port and installs malware on it. Once an unsuspecting mobile device user plugs their phone or tablet into the charging port, the malware automatically installs via a rogue USB cable connected to the charging station. This malware can then either steal data from the device or lock it down completely, allowing the criminal to demand a ransom to release the device.
In some cases, the malware can even take control of a device's operating system or install ransomware to demand money to unlock it. In other cases, the hacker might use the malware to steal data from the device, such as contacts, emails, and files. Once the user's information has been copied, the attacker can sell the data on the dark web.
Juice jacking is typically more common in high-density areas where people are in a rush and may be more likely to use public charging ports. It's also common in places where there are large crowds, such as public events, airports, and train stations.
To protect against juice jacking, experts advise avoiding using public charging stations altogether. Instead, carry a portable charger or connect the charging cable to a personal adapter. In addition, users can install antivirus software on their devices and avoid using public wifi networks when charging their devices.
Types of Juice Jacking:
Data Theft
One type of juice jacking that has become popular among cybercriminals is data theft. In this scenario, hackers use public charging stations or USB ports to gain access to a victim's mobile device and extract sensitive information like banking details, emails, and personal data. The process is swift and silent, and victims may not even realize the theft until they notice suspicious transactions or unusual account activity. While the convenience of public charging stations can be tempting, it's essential to avoid connecting to them as most do not have any security features to protect against such attacks.
Malware Installation
Another type of juice jacking is malware installation. In this scenario, hackers use public charging ports to load malicious software onto the victim's mobile device, which allows them to control the device remotely. Malware installation can give hackers access to sensitive information, including passwords and login credentials. Additionally, hackers can use the infected device as a launching pad to attack other networks. This attack is particularly effective as it can bypass firewalls, antivirus software, and even biometric sensors. Hence it is essential to use only personal charging devices and avoid public charging ports to avoid such attacks.
Multi-Device Attack
A multi-device attack is a type of juice jacking involving an external device, such as a fake charging station or a compromised USB port, to target multiple devices at once. This method is often used in high-traffic areas, such as airports, train stations, and shopping malls, where individuals may be in a hurry to charge their devices and could fall victim to the scam.
The attackers upload malware onto the compromised charging station, which is installed on any device connecting to the station. Once the malware is installed, the attackers access the user's data, including sensitive information such as passwords, bank details, and personal information.
Disabling Attack
A disabling attack is a type of juice jacking involving malicious code to disable a device or prevent it from functioning correctly. When an individual connects their device to a compromised charging station, the attacker installs software to disrupt the device's operation.
Sometimes, the attacker may lock the device and prevent the user from accessing it until they pay a ransom. In other cases, the attacker may altogether disable the device, causing the user to lose all their data. This type of attack can be particularly devastating for individuals who rely heavily on their devices for work or personal use. It is essential to exercise caution when charging devices in public places and to avoid using compromised charging stations whenever possible.
Tips to Protect Your Device from Juice Jacking:
Avoid Public Charging Stations
One of the biggest threats to your device's security is juice jacking. This occurs when you use public charging stations, which may contain malware or viruses hidden within the charging ports. This can compromise your device and allow unauthorized access to your personal data, contacts, and banking apps. It is recommended to use your charger whenever possible or carry a portable power bank to avoid juice jacking. If you must use a public charging station, make sure to use a cable that connects only to the USB port and not to any data transfer ports, and avoid using charging cables from unknown sources.
Use a Power Socket
Using a power socket to charge your device is safer than using public charging stations. Simply plug your charger into a power socket, and your phone will be charged without any risk of exposure to malware or viruses. Always use a charger that a reputable company makes, as generic chargers could also pose risks. Additionally, it is important to ensure that your phone is securely locked with a strong password, biometric or pattern lock, and to activate its security features such as a firewall, antivirus, and frequent software updates. Utilizing these measures can protect your device and ensure that your personal data remains safe and secure.
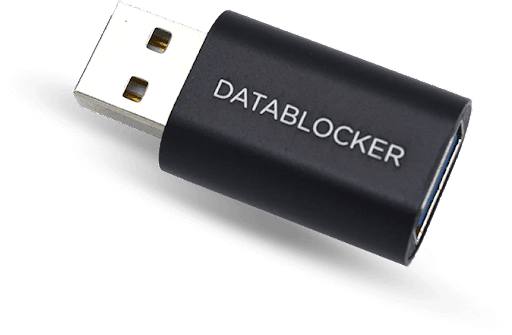
Use a USB Data Blocker
- What is a USB Data Blocker?
A USB data blocker is a small device that is used to protect your electronic devices from potential security threats. When you plug your phone or laptop into a public charging station or a foreign USB port, hackers can steal your data, install malware, or even remotely control your device. A USB data blocker blocks data transfer while allowing your device to charge.
- Why Do You Need USB Data Blockers?
A USB data blocker provides an essential layer of security for any tech user. In today's ever-increasing threats to our online security, being proactive with your privacy is crucial. USB data blockers are particularly handy when you are traveling and need to charge your device in a public place. USB data blockers are also useful for business travelers dealing with sensitive information. Using a USB data blocker, you can prevent potential data breaches, avoid cyber-attacks, and maintain your privacy and control over data when connected to a public wireless internet provider . With cyber security risks growing daily, using a USB data blocker is a simple but valuable way to minimize risk and enhance your safety.
- How to Test Your USB Data Blocker Is Working or Not?
USB data blockers are devices that are specifically designed to prevent data theft through USB charging ports. While they offer an effective solution to safeguarding your devices, it is crucial to ensure your USB data blocker is working correctly. Here are some ways you can test how your USB data blocker work:
- Use a USB meter to check the voltage of the USB data blocker. If it's working, it should display a voltage close to 5V.
- Connect your device to a power source with the USB data blocker in between. If the device charges as expected and doesn't transmit data, the blocker works successfully.
- Another way to test is by using forensic analysis software to check for any transferred data while using the blocker. If no data is found, it indicates that the blocker is indeed working.
- Testing your USB data blocker ensures that your devices are protected from potential data theft. It's always essential to verify the device's effectiveness before relying on it to protect your sensitive data.
Use Software Security Measures
Using software security measures to protect your device from juice jacking is important. One of the simplest measures is to ensure your device has up-to-date software and security patches. Additionally, you can use mobile device management (MDM) software to control which USB devices can connect to your phone, limit access to sensitive data, or block unauthorized downloads. There are also apps available, such as JuiceDefender, which can disable data transfer and only allow charging when connected to unauthorized USB devices. These measures can greatly reduce the risk of juice jacking and protect your personal data from being stolen.
Keep a Spare Charger or Power Bank with You
Another way to protect your device from juice jacking is to keep a spare charger or power bank. That way, you can avoid the temptation of using a public USB charging station. You should only use chargers and cables from trusted sources, as cheap and unbranded products can be unreliable and may damage your device. Additionally, a power bank can be a lifesaver when you're on the go and need to charge your device quickly. By using a trusted charger or power bank, you can eliminate the risk of data theft and ensure your device remains secure.
FAQ’s
Why Shouldn't You Charge Your Phone in USB Ports at the Airport?
Charging your phone at the Airport may seem like a convenient solution, but it comes at a cost. Hackers can use USB charging ports to transmit malware to your device, access your personal information or even install tracking software on your phone. To ensure your data's safety, charging your phone using a power outlet or bringing your portable charger is recommended.
What Devices Are Vulnerable to Juice Jacking Attacks?
Any device that uses a USB charging port is susceptible to juice-jacking attacks. This includes smartphones, tablets, laptops, and any other gadgets that can be charged through a USB connection. Juice jacking attacks are dangerous as they can give hackers full access to your device, steal personal data, and even install malware. Protect your devices by avoiding charging them in public places or using a USB Condom to block data transfer.
Conclusion
With the rise of "juice jacking," it is more important than ever to be proactive in protecting your digital life. Always check any public charging stations or cables before connecting them, and take extra precautions when you're out in public. Even if you know the people you are with, it is best to play it safe by bringing a portable charger and relying on your own device. Investigate any apps that ask for permission to access your device, ensure Bluetooth is off when you're not using it, disable cellular data at hotspots, and turn automatic logins off. These simple steps can increase security even further and give you peace of mind knowing that your device is protected against malicious attacks. Despite this being a relative niche attack method currently, remembering these tips will ensure your device is secured from whatever cyber threats arise in the present or future.


