Why Secure Internet Matters for Enterprise IT

Every IT Director knows the stakes are high when it comes to shielding sensitive healthcare data. In the Mid-Atlantic region, federal guidance from the Cybersecurity and Infrastructure Security Agency highlights that secure internet practices should protect not just systems but also data transmission and connectivity from unauthorized access and attacks. Modernizing network security means adopting a comprehensive organizational strategy that combines cutting-edge solutions with proactive safeguards, driving both regulatory compliance and operational continuity.
Table of Contents
- Defining Secure Internet for Enterprises
- Types of Enterprise Internet Security Solutions
- How Secure Connectivity Enables Compliance
- Protecting Sensitive Data Across Networks
- Risks of Poor Network Security Practices
Key Takeaways
| Point | Details |
|---|---|
| Comprehensive Security Strategy | Secure internet for enterprises requires a multi-layered strategy that goes beyond basic firewalls to protect digital assets. |
| Continuous Monitoring and Assessment | Regular system assessments and threat monitoring are essential to identify vulnerabilities and counteract emerging threats. |
| Compliance as a Component of Security | Meeting regulatory requirements should be integrated into security strategies to ensure holistic protection and operational resilience. |
| Proactive Risk Management | Organizations must adopt proactive measures like quarterly audits to identify and mitigate potential risks before they escalate. |
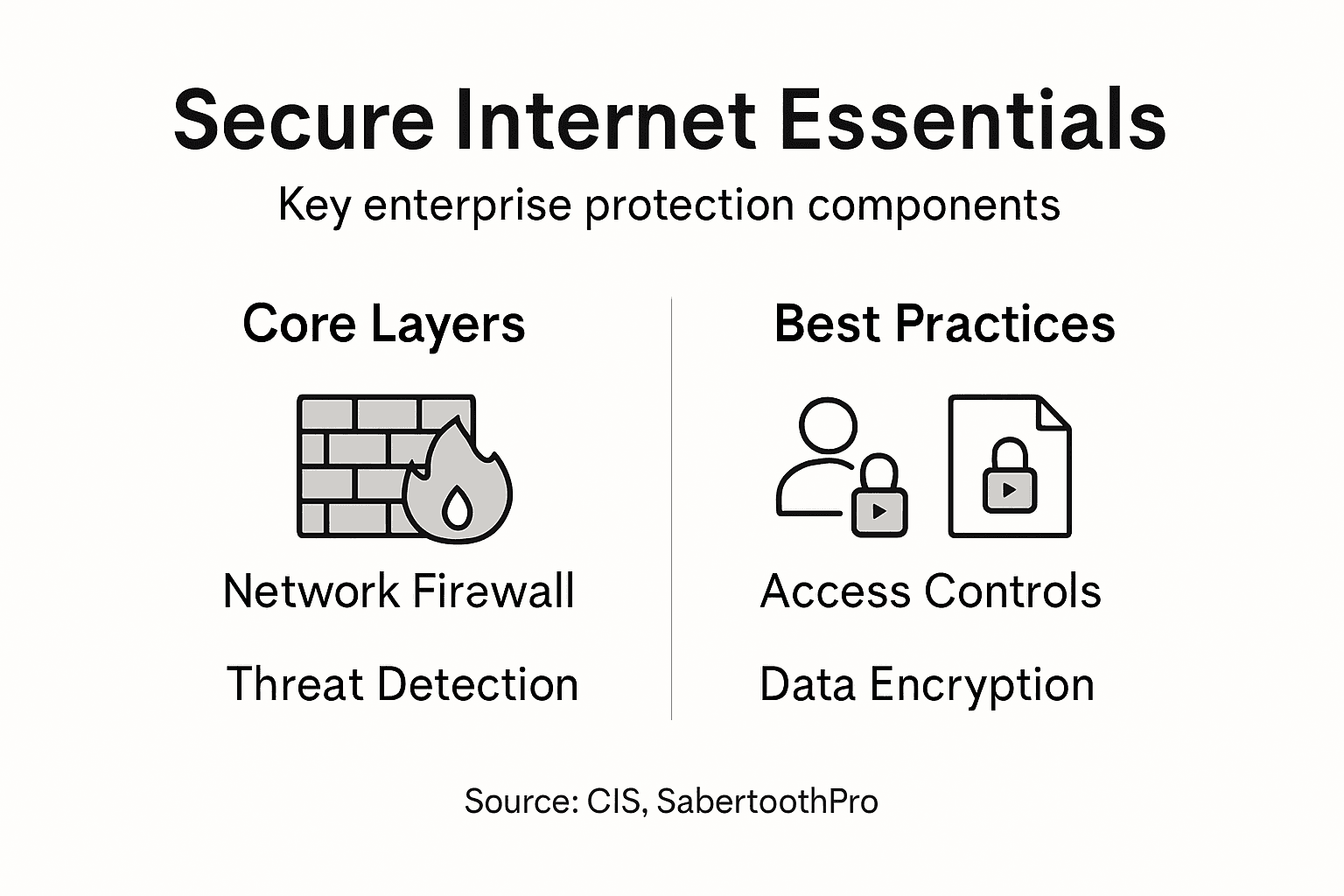
Defining Secure Internet for Enterprises
Secure internet for enterprises represents more than just network protection—it’s a comprehensive strategy designed to safeguard digital infrastructure, data transmission, and operational continuity. Enterprise internet security goes beyond basic firewalls, encompassing a holistic approach to defending against increasingly sophisticated cyber threats.
The Cybersecurity and Infrastructure Security Agency defines secure internet practices as systematic methods for protecting connectivity, preventing unauthorized access, and maintaining robust digital defense mechanisms. These practices typically involve multiple layers of protection:
- Implementing advanced network monitoring systems
- Establishing strict access control protocols
- Deploying real-time threat detection technologies
- Creating comprehensive incident response frameworks
- Maintaining continuous system vulnerability assessments
Enterprise internet security fundamentally requires understanding potential vulnerabilities and proactively addressing them before they can be exploited. The U.S. Department of Defense Cybersecurity Resource Guide emphasizes that secure connectivity isn’t just about technology—it’s about creating a resilient, adaptive security ecosystem that can respond dynamically to emerging digital risks.
Key Characteristics of Enterprise Internet Security:
- Multi-layered defense strategies
- Continuous monitoring and assessment
- Adaptive threat response mechanisms
- Compliance with industry regulatory standards
- Integration of human expertise with technological solutions
By treating secure internet as a comprehensive organizational strategy rather than a simple technical requirement, enterprises can effectively protect their most critical digital assets and maintain operational integrity.
Pro Tip: Conduct quarterly comprehensive security audits to identify and address potential network vulnerabilities before they become critical risks.
Types of Enterprise Internet Security Solutions
Enterprise internet security solutions represent a complex ecosystem of technologies designed to protect organizations from increasingly sophisticated cyber threats. Comprehensive security frameworks encompass multiple layers of defense, each addressing different aspects of digital infrastructure protection.
The primary categories of enterprise internet security solutions include:
-
Network Security Solutions:
- Firewalls
- Intrusion Detection Systems (IDS)
- Intrusion Prevention Systems (IPS)
- Network segmentation tools
-
Endpoint Protection:
- Antivirus software
- Endpoint Detection and Response (EDR)
- Mobile device management
- Zero trust endpoint solutions
-
Data Protection Technologies:
- Encryption systems
- Data loss prevention (DLP) tools
- Secure cloud storage solutions
- Backup and recovery platforms
The Department of Defense cybersecurity guide highlights that modern enterprise security requires an integrated approach that combines technological solutions with strategic human oversight. Adaptive security architectures enable organizations to respond dynamically to emerging threats, moving beyond traditional static defense mechanisms.
Here’s a summary of how different enterprise internet security solutions address key business needs:
| Solution Type | Primary Advantage | Typical Business Impact |
|---|---|---|
| Network Security | Monitors and segments data | Reduces internal threats |
| Endpoint Protection | Defends user devices | Mitigates external breaches |
| Data Protection Tech | Encrypts and safeguards data | Ensures compliance, reputation |
Key considerations when selecting enterprise internet security solutions include:
- Scalability of security infrastructure
- Compatibility with existing technology stack
- Comprehensive threat monitoring capabilities
- Regulatory compliance requirements
- Cost-effectiveness and resource optimization
Advanced Security Frameworks now incorporate artificial intelligence and machine learning to predict and prevent potential security breaches before they occur. This proactive approach represents a significant evolution in enterprise cybersecurity strategies.

Pro Tip: Implement a holistic security assessment every six months to identify potential vulnerabilities and ensure your security solutions remain current and effective.
How Secure Connectivity Enables Compliance
Compliance in enterprise environments requires more than just meeting minimum regulatory standards—it demands a comprehensive approach to network security and data protection. Comprehensive cybersecurity frameworks play a crucial role in helping organizations navigate complex regulatory landscapes while maintaining robust digital infrastructure.
Key compliance requirements typically involve multiple dimensions of secure connectivity:
-
Data Protection Standards:
- Encryption of sensitive information
- Secure data transmission protocols
- Access control mechanisms
- Audit trail documentation
-
Regulatory Framework Alignment:
- HIPAA compliance for healthcare
- PCI DSS for financial transactions
- GDPR for international data handling
- NIST security guidelines
The Center for Internet Security emphasizes that secure connectivity serves as a foundational element in meeting diverse regulatory mandates. By implementing comprehensive security controls, organizations can simultaneously address multiple compliance requirements while protecting critical digital assets.
Complex regulatory environments demand a strategic approach to connectivity that includes:
Compare major regulatory frameworks and their focus areas for enterprise compliance:
| Regulation | Industry Focus | Core Security Requirement | Penalty for Non-Compliance |
|---|---|---|---|
| HIPAA | Healthcare | Patient data confidentiality | Hefty fines, legal action |
| PCI DSS | Finance | Cardholder data protection | Loss of payment processing |
| GDPR | Global business | Personal data privacy | Up to 4% global turnover |
| NIST | Cross-industry | Security controls baseline | Reduced federal contracting |
- Continuous security monitoring
- Robust access management
- Comprehensive incident response planning
- Regular vulnerability assessments
- Documented security governance
Adaptive Security Architecture enables enterprises to create flexible compliance strategies that evolve with changing regulatory landscapes. This approach transforms compliance from a static checklist into a dynamic, integrated component of organizational strategy.
Secure connectivity is not just about meeting regulations—it’s about building a resilient digital ecosystem that protects your organization’s most valuable assets.
Pro Tip: Develop a cross-functional compliance team that includes IT, legal, and security professionals to create a holistic approach to regulatory requirements.
Protecting Sensitive Data Across Networks
In the digital age, protecting sensitive data across enterprise networks has become increasingly complex and critical. Enterprise data protection strategies must evolve continuously to address sophisticated cyber threats and maintain the confidentiality of organizational information.
Comprehensive data protection requires a multi-layered approach encompassing several key dimensions:
-
Data Encryption:
- Encryption of data in transit
- Encryption of data at rest
- End-to-end encryption protocols
- Key management systems
-
Access Control Mechanisms:
- Multi-factor authentication
- Role-based access controls
- Privileged access management
- Identity verification protocols
The Harvard Privacy & Security guidance emphasizes that data lifecycle management is crucial in maintaining robust security across enterprise networks. By implementing strategic controls at each stage of data handling, organizations can significantly reduce potential vulnerabilities and unauthorized access risks.
Enterprise data protection strategies should focus on:
- Minimizing data collection
- Implementing strict access controls
- Monitoring data transmission channels
- Creating comprehensive incident response plans
- Regularly updating security protocols
Advanced Network Security integrates machine learning and artificial intelligence to predict and prevent potential data breaches before they can compromise sensitive information. This proactive approach transforms data protection from a reactive measure to a predictive strategy.
Effective data protection is not about building impenetrable walls, but creating intelligent, adaptive systems that can recognize and neutralize threats in real-time.
Pro Tip: Conduct periodic data sensitivity assessments to classify and prioritize protection strategies for different types of organizational information.
Risks of Poor Network Security Practices
Enterprise networks face increasingly sophisticated cyber threats that can exploit even minor vulnerabilities in network security infrastructure. Infrastructure security risks represent significant potential for organizational disruption and financial damage when left unaddressed.
The most critical network security vulnerabilities include:
-
Software and System Vulnerabilities:
- Unpatched legacy systems
- Outdated security protocols
- Unsupported operating systems
- Unmanaged software dependencies
-
Access Control Weaknesses:
- Weak password policies
- Lack of multi-factor authentication
- Excessive user privileges
- Inadequate user access reviews
The EC-Council cybersecurity analysis reveals that poor security practices can expose organizations to devastating cyber threats, including:
- Malware infiltration
- Ransomware attacks
- Data breaches
- Persistent system compromises
- Financial and reputational damage
Cybersecurity Threat Landscape demonstrates that organizations with weak network security practices are essentially leaving their digital doors wide open to malicious actors. These vulnerabilities can lead to catastrophic consequences that extend far beyond immediate technical disruptions.
Network security is not just an IT problem—it’s a critical business risk management issue that demands comprehensive, proactive strategies.
Pro Tip: Implement a quarterly comprehensive security audit that systematically evaluates and patches all potential network vulnerabilities across your entire digital infrastructure.
Secure Your Enterprise Internet with SabertoothPro Solutions
Enterprises face ongoing challenges such as adapting to multi-layered defense strategies and ensuring continuous threat monitoring. The risk of poor network security can lead to costly breaches and compliance issues. SabertoothPro understands these critical pain points and offers tailored solutions that align with key concepts like zero-trust frameworks and adaptive security architectures. Our advanced Titan WiFi devices deliver reliable, high-speed connectivity while supporting secure and scalable network environments.
Experience the benefit of secure, enterprise-grade internet through our specialized Titan WiFi Hotspot Plans designed for demanding business needs. Don’t risk lapses in protection or slow infrastructure. Visit SabertoothPro.com today to explore solutions that combine cutting-edge technology with expert consultation. Protect your business now with proven tools built to keep your digital ecosystem resilient and compliant.
Frequently Asked Questions
What are the key components of secure internet for enterprises?
Secure internet for enterprises includes advanced network monitoring systems, strict access control protocols, real-time threat detection technologies, incident response frameworks, and continuous system vulnerability assessments.
Why is it important for enterprises to implement multi-layered defense strategies?
Multi-layered defense strategies are crucial because they provide comprehensive protection against diverse and sophisticated cyber threats, ensuring that no single vulnerability can lead to a security breach.
How do compliance requirements impact enterprise internet security?
Compliance requirements necessitate that enterprises adhere to specific security standards, such as data encryption and access control mechanisms, which help protect sensitive information and avoid hefty penalties for non-compliance.
What role does data protection play in secure internet strategies?
Data protection is vital as it involves encryption, access controls, and monitoring to safeguard sensitive information across networks, ensuring organizational data confidentiality and integrity.
