Wireless Connectivity Guide: Set Up Secure and Reliable Networks
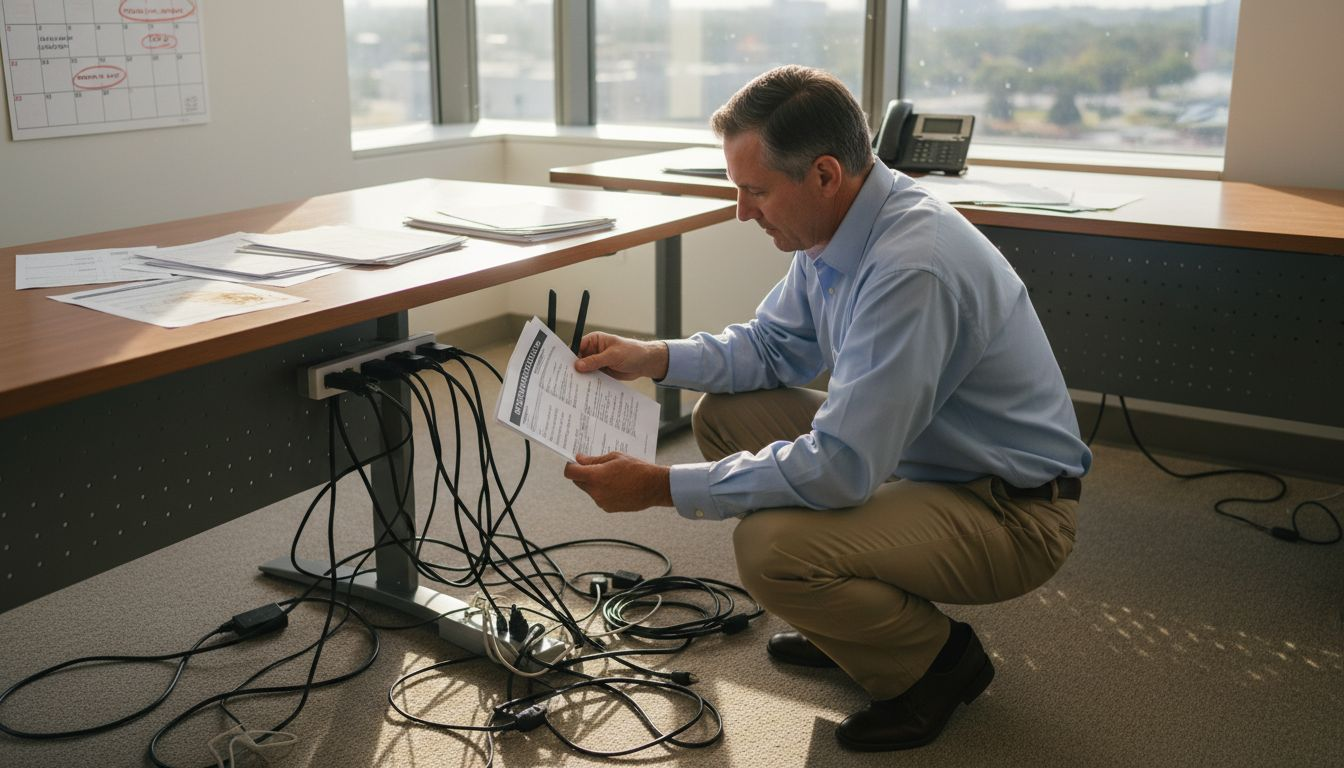
Managing wireless connectivity for remote teams and IoT devices can quickly reveal the limits of your current network. For IT leaders at healthcare and retail organizations across the Mid-Atlantic, ensuring dependable coverage means more than installing new hardware. It starts with a precise evaluation of your network’s requirements and environment, followed by strategic choices in devices, security settings, and ongoing performance validation. Discover how a comprehensive network assessment leads to scalable solutions tailored for your operations.
Table of Contents
- Step 1: Assess Network Requirements And Environment
- Step 2: Select Optimal Devices And Internet Plans
- Step 3: Configure Wireless Hardware And Security Settings
- Step 4: Integrate IoT Devices And Business Applications
- Step 5: Verify Performance And Ensure Ongoing Reliability
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Assess Network Requirements Carefully | Thoroughly analyze user density, bandwidth, and coverage areas to create an effective wireless network design. |
| 2. Choose the Right Devices and Plans | Select wireless devices and internet plans that balance performance, reliability, and cost-effectiveness to meet operational needs. |
| 3. Prioritize Robust Security Configurations | Implement comprehensive security protocols, including encryption and access control, to protect your network from cyber threats. |
| 4. Integrate IoT Devices Effectively | Ensure compatibility and security of IoT devices to enhance automation and real-time data usage in business operations. |
| 5. Continuously Monitor Network Performance | Regularly test and evaluate network reliability to identify issues quickly and maintain a high-quality connection. |
Step 1: Assess Network Requirements and Environment
Assessing your network requirements is the critical first step in designing a robust and reliable wireless infrastructure. This process involves understanding your specific environment, operational needs, and technical constraints to create a network solution that performs precisely where and how you need it.
The assessment begins with a comprehensive requirements decomposition analysis. This means breaking down your organization’s connectivity needs into clear, achievable objectives. Start by mapping out key considerations:
- Current Network Topology: Document existing network architecture
- User Density: Calculate number of simultaneous users and devices
- Bandwidth Requirements: Estimate data transfer and performance needs
- Coverage Areas: Identify physical spaces requiring wireless connectivity
Your network environment assessment should also include detailed infrastructure design standards, which encompass critical elements like:
- Physical room configurations
- Environmental control parameters
- Electrical infrastructure capabilities
- Wireless signal strength mapping
Effective network design requires understanding both technological capabilities and organizational constraints.
By systematically evaluating these factors, you’ll develop a comprehensive blueprint for your wireless network that aligns with operational goals and technical limitations.

Pro tip: Consider involving stakeholders from different departments to capture a holistic view of network requirements during your initial assessment.
Step 2: Select Optimal Devices and Internet Plans
Selecting the right wireless devices and internet plans is crucial for ensuring seamless connectivity that meets your specific operational needs. Your goal is to find a solution that balances performance, reliability, and cost-effectiveness.
When choosing an internet service plan, consider these critical factors:
- Connection Speed: Determine bandwidth requirements for your specific use case
- Data Limitations: Evaluate monthly data caps and potential overage charges
- Contract Terms: Review length of commitment and potential early termination fees
- Technology Compatibility: Ensure devices support your chosen network infrastructure
Your device selection process should involve a comprehensive evaluation of several key parameters:
- Network frequency compatibility (4G/5G)
- Device performance specifications
- Battery life and portability
- Security features and encryption capabilities
Successful connectivity relies on matching your technological requirements with the right hardware and service plan.
Prioritize providers offering flexible plans that can scale with your organization’s evolving connectivity demands. Compare multiple options, read user reviews, and request detailed technical specifications before making a final decision.
Pro tip: Consider scheduling technical consultations with potential providers to discuss custom networking solutions tailored to your specific environment.
Step 3: Configure Wireless Hardware and Security Settings
Configuring your wireless hardware and security settings is a critical step in protecting your network infrastructure from potential cyber threats and unauthorized access. This process involves implementing robust security protocols that safeguard your organization’s digital communication channels.
Start by implementing comprehensive wireless security protocols that protect your network from potential intrusions:
- Authentication: Set up multi-factor verification processes
- Encryption: Enable WPA3 security standards
- Access Control: Configure granular user permissions
- Network Segmentation: Isolate sensitive network segments
Your hardware configuration should address several key security dimensions:
- Disable default administrator credentials
- Update firmware regularly
- Configure firewall settings
- Implement intrusion detection systems
Effective wireless security is a proactive, multilayered approach that combines technological controls with strategic configuration.
Important security practices include managing device discoverable modes, disabling unnecessary network services, and creating complex passwords that meet current cybersecurity recommendations. Regularly audit and update your security configurations to stay ahead of emerging threats.
Here’s a comparison of key wireless network security measures and their business impact:
| Security Measure | Main Purpose | Business Impact |
|---|---|---|
| Multi-factor Authentication | Prevent unauthorized access | Reduces risk of breaches |
| WPA3 Encryption | Protect data in transit | Strengthens regulatory compliance |
| Access Control | Restrict user permissions | Minimizes insider threats |
| Intrusion Detection | Monitor suspicious activity | Enables early threat response |
Pro tip: Schedule quarterly security audits to identify and address potential vulnerabilities in your wireless network infrastructure.
Step 4: Integrate IoT Devices and Business Applications
Integrating Internet of Things (IoT) devices into your business infrastructure transforms operational capabilities by enabling real-time monitoring, automation, and data-driven decision-making. Your goal is to create a seamless, intelligent network that enhances productivity and provides actionable insights.
When implementing IoT architectures, focus on these critical integration strategies:
- Device Compatibility: Ensure cross-platform communication protocols
- Data Standardization: Create uniform data collection and processing methods
- Security Protocols: Implement robust authentication and encryption
- Scalability: Design flexible infrastructure supporting future expansions
Your integration process should address multiple key dimensions:
- Map existing business workflows
- Identify potential IoT sensor deployment points
- Select interoperable device platforms
- Develop centralized management interfaces
Successful IoT integration requires a holistic approach that balances technological capability with strategic business objectives.
Prioritize solutions that offer seamless data exchange, enable predictive maintenance, and provide real-time analytics across your organization’s critical operational areas. Continuously evaluate and refine your IoT ecosystem to maintain competitive advantage.

This table summarizes common IoT deployment challenges and effective solutions:
| IoT Challenge | Typical Cause | Effective Solution |
|---|---|---|
| Data Silos | Incompatible platforms | Use standardized protocols |
| Security Risks | Weak device safeguards | Enable end-to-end encryption |
| Scalability Limitations | Poor infrastructure design | Plan for modular architecture |
| Integration Issues | Legacy system constraints | Select interoperable devices |
Pro tip: Conduct pilot tests with a small subset of IoT devices before full-scale deployment to validate integration strategies and identify potential challenges.
Step 5: Verify Performance and Ensure Ongoing Reliability
Ensuring the continuous performance and reliability of your wireless network requires systematic testing and proactive monitoring. Your objective is to create a robust infrastructure that maintains high-quality connectivity and quickly addresses potential issues.
Implement comprehensive network reliability testing to validate your network’s performance across multiple dimensions:
- Fault Tolerance: Establish redundancy and backup communication paths
- Quality of Service: Prioritize critical network traffic
- Performance Metrics: Monitor latency, bandwidth, and connection stability
- Security Validation: Continuously test network defense mechanisms
Your verification process should include these critical steps:
- Conduct regular diagnostic scans
- Perform over-the-air performance assessments
- Simulate high-traffic scenarios
- Test failover and recovery protocols
Network reliability is not a destination but a continuous journey of monitoring, testing, and improvement.
Utilize advanced diagnostic tools to simulate real-world conditions and identify potential vulnerabilities before they impact your operational capabilities. Regular performance audits help maintain a resilient and responsive network infrastructure.
Pro tip: Develop a standardized performance reporting framework that tracks key network metrics and enables rapid response to emerging connectivity challenges.
Build Secure and Reliable Wireless Networks with SabertoothPro Solutions
Designing a wireless network that meets your specific connectivity needs while maintaining top-notch security can feel overwhelming. This article highlighted key challenges like choosing the right devices, configuring robust security protocols, and ensuring ongoing network reliability. If you want to overcome these hurdles with proven technology that adapts to your environment and scale, SabertoothPro.com has you covered with expertly curated products and tailored internet plans.
Secure your network starting today by exploring high-performance 4G and 5G hotspots, powerful routers, and seamless Wi-Fi solutions like those found in our Titan WiFi collection.
Discover how our solutions can simplify your network infrastructure while enhancing security and speed. Visit SabertoothPro.com now, explore our WiFi extenders to expand your coverage, and take the next step toward a more reliable, secure wireless environment tailored to your unique needs.
Frequently Asked Questions
How do I assess my network requirements when setting up a wireless connectivity solution?
Assess your network requirements by conducting a detailed analysis of your current network topology, user density, bandwidth needs, and coverage areas. Map these factors based on your organization’s operational goals to develop a tailored network blueprint.
What should I consider when selecting internet plans for my wireless network?
When selecting internet plans, evaluate connection speed, data limitations, contract terms, and technology compatibility. Choose plans that align with your estimated bandwidth requirements for seamless connectivity, potentially upgrading to higher tiers based on future needs.
What are the essential steps to configure wireless hardware and security settings?
To configure your wireless hardware, implement strong security protocols such as multi-factor authentication and WPA3 encryption. Ensure you regularly update firmware and perform routine audits to maintain your network’s security posture and minimize vulnerabilities.
How can I successfully integrate IoT devices into my wireless network?
Integrate IoT devices by ensuring device compatibility, employing standardized data collection methods, and implementing robust security protocols. Map out existing workflows and identify optimal sensor deployment points for effective integration and automation.
What actions can I take to verify the performance and reliability of my wireless network?
To verify performance, conduct diagnostic scans, simulate high-traffic scenarios, and monitor key performance metrics such as latency and connection stability. Schedule these tests regularly to maintain a responsive and resilient wireless infrastructure.
