IoT Security Explained: Protecting Enterprise Devices

Securing remote devices across your enterprise is more than a technical challenge—it is a daily concern for IT leaders navigating complex digital ecosystems. As organizations in the Mid-Atlantic region expand their connected infrastructure, the risks linked to weak authentication, unpatched firmware, and insecure network segmentation grow. This article offers practical guidance and actionable strategies for holistic endpoint-to-cloud protection and robust compliance frameworks, helping you develop reliable connectivity and management approaches for every device under your control.
Table of Contents
- What IoT Security Means for Enterprises
- Types of IoT Threats and Attack Vectors
- Core Protections for Connected Device Security
- Compliance and Regulatory Considerations in the U.S.
- Risks, Costs, and Mistakes to Avoid
Key Takeaways
| Point | Details |
|---|---|
| Holistic IoT Security Approach | Enterprises must implement a comprehensive, multilayered security strategy that protects all points of vulnerability. |
| Proactive Threat Management | Continuous monitoring and regular updates, including patch management, are vital to combat sophisticated IoT security threats. |
| Regulatory Compliance | Compliance with established frameworks, like NIST guidelines, is essential for minimizing risks and avoiding penalties. |
| Common Pitfalls to Avoid | Avoid using default passwords and neglecting updates to reduce vulnerability; proactive risk management is crucial for effective security. |
What IoT Security Means for Enterprises
Enterprise IoT security represents a comprehensive approach to protecting interconnected digital infrastructure across multiple technological domains. Unlike traditional network security, IoT security involves holistic endpoint-to-cloud protection that addresses vulnerabilities throughout the entire device lifecycle.
The IoT ecosystem for enterprises is complex, encompassing numerous interconnected components that create potential cybersecurity risks. These risks emerge from diverse sources including hardware vulnerabilities, communication protocol weaknesses, and backend platform exposures. Enterprises must develop multilayered security strategies that protect against threats at every potential entry point.
Critical IoT security considerations for enterprises include:
- Securing device authentication mechanisms
- Implementing robust encryption protocols
- Managing firmware and software updates
- Establishing network segmentation
- Controlling remote access permissions
- Monitoring device communication channels
Specifically, enterprises face significant cybersecurity challenges with IoT devices, such as weak default passwords, unpatched firmware, and insufficient network isolation. Addressing these risks requires proactive management and strategic security implementations that go beyond traditional IT security approaches.
Pro tip: Always change default device credentials immediately upon deployment and implement a rigorous patch management system for all IoT infrastructure.
Types of IoT Threats and Attack Vectors
Enterprise IoT infrastructure faces a complex landscape of cybersecurity threats that target multiple technological layers. Common IoT attack vectors exploit systematic vulnerabilities across device hardware, communication protocols, and network architectures, creating significant security challenges for organizations.
The most prevalent IoT threat categories include:
- Credential Compromise: Attacks leveraging weak or default passwords
- Network Intrusion: Unauthorized access through unsecured communication channels
- Malware Injection: Inserting malicious code into device firmware or software
- Data Interception: Capturing unencrypted network communications
- Lateral Movement: Exploiting compromised devices to access broader network infrastructure
Specifically, IoT devices face diverse threats modeled across multiple attack taxonomies, including sophisticated methods like botnet creation, brute force password attacks, and side-channel exploitations. These attacks target vulnerabilities in device authentication, communication protocols, and software layers, demonstrating the multifaceted nature of IoT security risks.
Enterprise security teams must develop comprehensive strategies that address these complex threat landscapes by implementing robust authentication mechanisms, continuous monitoring, and proactive vulnerability management across their entire IoT ecosystem.
Here’s a comparison of IoT threats and recommended enterprise defense strategies:
| Threat Type | Attack Example | Recommended Defense |
|---|---|---|
| Credential Compromise | Brute-force password attack | Enforce strong authentication |
| Network Intrusion | Unsecured port exploitation | Apply network segmentation |
| Malware Injection | Firmware with hidden malware | Run continuous device scans |
| Data Interception | Packet sniffing attack | Use end-to-end encryption |
| Lateral Movement | Botnet spread | Isolate IoT segments |
Pro tip: Implement a zero-trust security model that validates every device connection and restricts network access based on strict, continuously verified permissions.
Core Protections for Connected Device Security
Enterprise IoT security demands a comprehensive, multilayered approach to protecting connected devices across complex technological ecosystems. Implementing robust cybersecurity best practices requires strategic planning and continuous monitoring to mitigate potential vulnerabilities and protect critical infrastructure.
Key core protections for connected device security include:
- Device Configuration: Establishing secure baseline configurations
- Authentication Management: Implementing multi-factor authentication
- Access Control: Restricting network permissions and user privileges
- Patch Management: Applying timely software and firmware updates
- Network Segmentation: Isolating IoT devices from critical network segments
- Encryption: Securing communication channels and data transmissions
Critical security controls provide a structured framework for enterprises to systematically address IoT device vulnerabilities. These controls emphasize maintaining comprehensive asset inventories, enforcing strong authentication mechanisms, and implementing continuous vulnerability management strategies that adapt to evolving technological landscapes.

Successful IoT security requires a proactive approach that integrates technical controls, organizational policies, and ongoing risk assessments to create a resilient defense against sophisticated cyber threats.
Pro tip: Conduct quarterly comprehensive security audits of all connected devices, including a full inventory review and vulnerability assessment to identify and remediate potential security gaps.
Compliance and Regulatory Considerations in the U.S.
The U.S. regulatory landscape for IoT security has evolved significantly, with federal agencies establishing comprehensive guidelines to protect critical technological infrastructure. IoT Cybersecurity Improvement Act of 2020 represents a pivotal moment in mandating minimum security standards for connected devices across government systems.
Key regulatory compliance requirements for enterprises include:
- Device Inventory: Comprehensive tracking of all IoT devices
- Security Standardization: Adherence to NIST security guidelines
- Risk Management: Continuous evaluation of device security capabilities
- Procurement Protocols: Implementing secure-by-design acquisition strategies
- Lifecycle Management: Systematic security monitoring from deployment to retirement
NIST Special Publication establishes critical cybersecurity requirements that provide a structured framework for federal agencies and private enterprises. These guidelines emphasize proactive risk management, promoting security integration throughout the entire device lifecycle and encouraging organizations to develop robust, adaptive security strategies.
Compliance is not merely a checkbox exercise but a dynamic process requiring continuous assessment, updates, and alignment with evolving technological and regulatory landscapes. Enterprises must develop flexible frameworks that can quickly adapt to emerging federal guidelines and technological shifts.
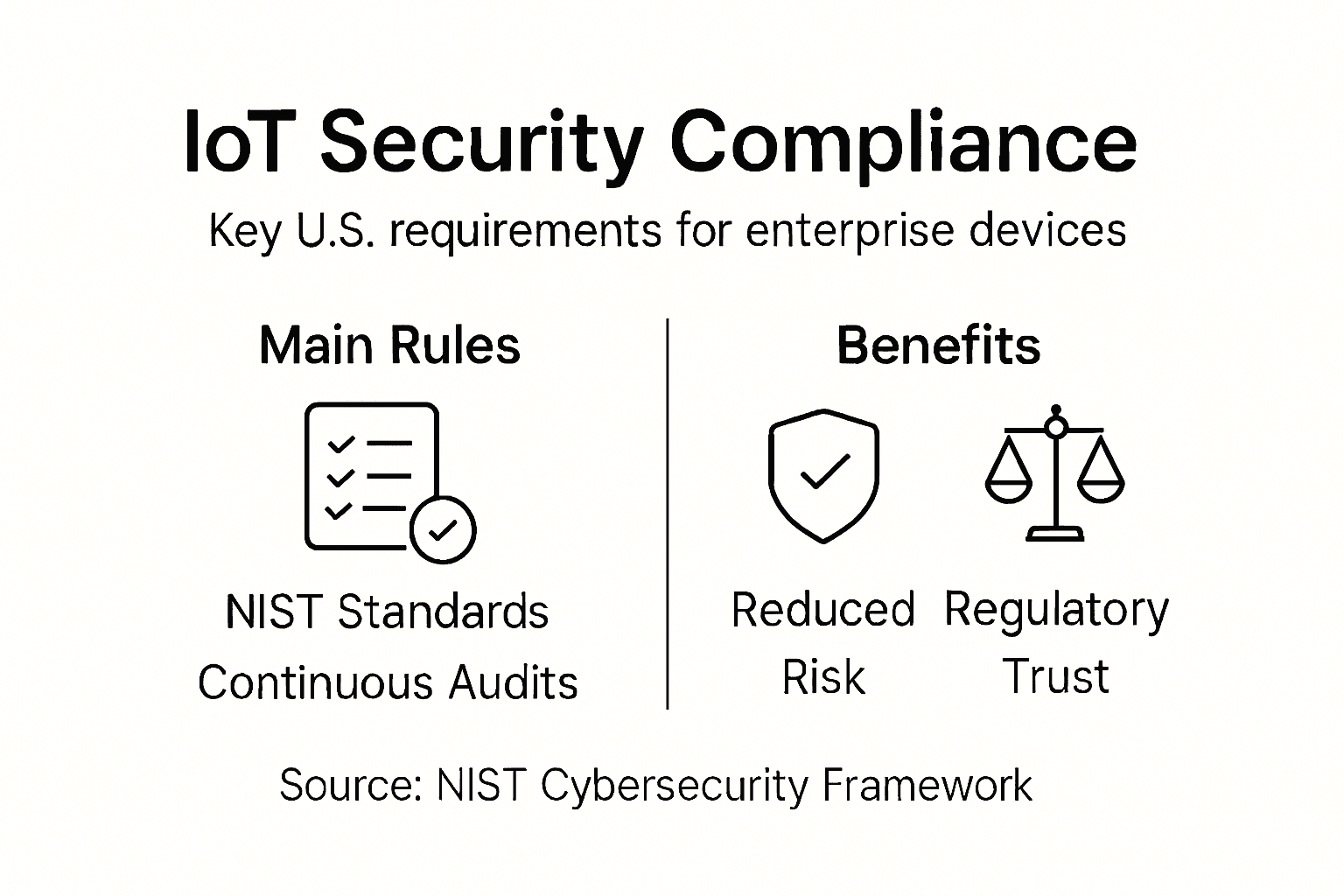
This table summarizes key U.S. IoT compliance elements and their business benefits:
| Compliance Requirement | Purpose | Business Benefit |
|---|---|---|
| Device Inventory | Track all endpoints | Reduces blind spots |
| Security Standardization | Meet NIST guidelines | Ensures audit readiness |
| Risk Management | Ongoing vulnerability checks | Minimizes regulatory penalties |
| Procurement Protocols | Secure device sourcing | Lowers supply chain risk |
| Lifecycle Management | End-to-end oversight | Sustains long-term compliance |
Pro tip: Develop a centralized compliance tracking system that automatically maps your IoT devices against the latest NIST and federal security requirements.
Risks, Costs, and Mistakes to Avoid
Cybersecurity risks in IoT environments have become increasingly sophisticated, presenting complex challenges for enterprises seeking to protect their digital infrastructure. The rapid proliferation of connected devices has exponentially expanded potential attack surfaces, making comprehensive security strategies more critical than ever.
Common mistakes that dramatically increase organizational vulnerability include:
- Credential Negligence: Using default or weak passwords
- Update Avoidance: Ignoring critical firmware and software patches
- Network Exposure: Failing to implement proper network segmentation
- Communication Vulnerability: Transmitting data without robust encryption
- Access Management: Inadequate authentication and permission controls
- Monitoring Gaps: Insufficient logging and anomaly detection mechanisms
IoT security best practices emphasize proactive risk mitigation through systematic approaches to device management. Enterprises face potentially devastating consequences from security breaches, including operational disruptions, financial losses, regulatory penalties, and long-term reputational damage that can far exceed the immediate costs of implementing robust security measures.
Effective risk management requires a holistic approach that integrates technological solutions, organizational policies, and continuous learning. Security is not a one-time implementation but an ongoing process of adaptation, assessment, and improvement.
Pro tip: Conduct monthly comprehensive security audits that simulate potential breach scenarios and systematically evaluate your IoT infrastructure’s resilience against emerging threats.
Strengthen Your Enterprise IoT Security with SabertoothPro
Enterprises face complex challenges securing IoT devices against evolving threats like credential compromise and network intrusion. The article highlights the urgent need for comprehensive protections including robust authentication, encryption, and continuous monitoring. If you are concerned about vulnerabilities caused by weak default passwords or insufficient network segmentation SabertoothPro offers tailored solutions to safeguard your IoT ecosystem.
Benefit from our IoT Connectivity and Device Management built for scale and reliability combined with next-gen security services such as SOC-as-a-Service and Zero-Trust Frameworks that proactively defend your entire infrastructure. Our advanced high-speed internet options including 4G LTE and 5G hotspots ensure seamless, secure connections even in rural or mobile environments.
Protect your enterprise devices today with trusted solutions designed to meet rigorous compliance and security standards. Visit SabertoothPro.com to explore IoT security and connectivity offerings that can transform your security posture. Book a consultation now to start building a resilient and future-proof IoT infrastructure.
Frequently Asked Questions
What is IoT security for enterprises?
IoT security for enterprises refers to the comprehensive approach to protecting interconnected digital infrastructure, covering endpoint-to-cloud security measures to address vulnerabilities throughout the device lifecycle.
What are the main types of threats to enterprise IoT devices?
The main types of threats to enterprise IoT devices include credential compromise, network intrusion, malware injection, data interception, and lateral movement, each exploiting different vulnerabilities in the system.
How can enterprises protect their IoT devices?
Enterprises can protect their IoT devices by implementing strong authentication mechanisms, network segmentation, regular firmware updates, robust encryption protocols, and continuous monitoring of device communication channels.
What are the compliance requirements for IoT security in the U.S.?
In the U.S., compliance requirements for IoT security include comprehensive device inventory, adherence to NIST security guidelines, continuous risk management, secure procurement protocols, and systematic lifecycle management to ensure device security throughout its lifecycle.
Recommended
- Cyber Threats for Small Business: Preventing Disruption
- 7 Enterprise Cloud Hosting Benefits for IT Leaders
