Role of network optimization for cloud and IoT in 2026

Many IT managers think network optimization is just about speed, but it’s equally about security, scalability, and cost management. Mid-sized enterprises face unique challenges optimizing cloud and IoT networks amid rising complexity. This guide explains advanced techniques and practical steps for effective network optimization that enhance connectivity, security, and operational efficiency across your entire infrastructure.
Table of Contents
- Understanding Network Optimization: Foundations And Importance
- Common Misconceptions About Network Optimization
- Advanced Network Optimization Techniques: AI And Edge Computing
- Security Considerations In Network Optimization
- Techniques For IoT Network Optimization
- Cloud Network Optimization Strategies
- Conceptual Framework For Network Optimization In Cloud And IoT
- Implementing Network Optimization: Practical Steps For Mid-Sized Enterprises
- Optimize Your Enterprise Network With Expert Solutions
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Comprehensive optimization | Network optimization enhances security, scalability, and cost-efficiency alongside performance. |
| Advanced technologies | AI and edge computing are pivotal techniques improving cloud and IoT network efficiency. |
| Integrated security | Security must be integrated from the start using zero-trust models and SASE frameworks. |
| Tailored strategies | Customized optimization approaches for mid-sized enterprises help avoid common pitfalls and maximize benefits. |
| Measurable impact | Operational metrics like latency, throughput, and security incidents effectively measure optimization success. |
Understanding network optimization: foundations and importance
Network optimization involves improving network performance, security, scalability, and cost-efficiency specifically for cloud and IoT systems. It’s not a single fix but a holistic approach addressing connectivity, protection, and resource allocation simultaneously.
Mid-sized enterprises face distinct challenges that large corporations and small businesses don’t encounter. Device proliferation creates massive complexity as thousands of IoT sensors, cloud applications, and edge devices compete for bandwidth. Dynamic traffic patterns shift unpredictably as workloads move between on-premises infrastructure and cloud environments. Managing hybrid architectures requires balancing legacy systems with modern cloud-native applications.
Inefficient networks create cascading problems throughout your organization:
- Latency spikes disrupt real-time applications and frustrate users
- Security vulnerabilities expose sensitive data and intellectual property
- Higher operational costs drain budgets through wasted bandwidth and inefficient resource allocation
- Innovation stalls when infrastructure can’t support new initiatives
Optimizing connectivity and security across cloud services and IoT devices is essential for growth and resilience. Understanding these foundations through business connectivity essentials for IT leaders prepares you to implement effective strategies. Technologies like SD-WAN for distributed locations demonstrate how targeted optimization transforms network performance.
Common misconceptions about network optimization
Myth: Network optimization is only about increasing internet speed.
Fact: Speed matters, but optimization equally involves enhancing security, scalability, and cost management. A faster network that’s vulnerable to breaches or can’t scale with business growth creates more problems than it solves.
Myth: Security can be added after optimization is complete.
Fact: Embedding security frameworks like zero-trust and SASE during optimization is critical. Surveys show 60% of IT managers underestimate security integration as part of optimization. Bolting on protection afterward creates gaps attackers exploit.
Myth: One-size-fits-all solutions suffice regardless of enterprise size or IoT complexity.
Fact: Optimization must be tailored to your unique network characteristics. What works for a Fortune 500 company with unlimited resources won’t fit a mid-sized enterprise managing hundreds of IoT devices on constrained budgets.
“The biggest mistake IT managers make is treating network optimization as a purely technical speed upgrade instead of a strategic business enabler spanning security, costs, and agility.”
Correcting these misconceptions leads to more effective planning and implementations. When you understand optimization’s true scope, you can allocate resources appropriately and set realistic expectations with stakeholders.
Advanced network optimization techniques: AI and edge computing
AI tools enable real-time traffic analysis, predictive maintenance, and automated optimization decisions that humans can’t match at scale. AI-powered network optimization reduces latency by 25% and increases throughput by 30% through real-time traffic management. Machine learning algorithms detect patterns in network behavior, predict congestion before it occurs, and automatically reroute traffic to maintain performance.

Edge computing processes data near IoT devices to minimize latency and reduce backhaul bandwidth. Instead of sending every sensor reading to centralized cloud servers, edge nodes handle local processing and only transmit critical insights. Edge computing cuts latency by 30% and bandwidth usage by 40% by processing IoT data locally, improving resilience when connectivity to central systems fails.
Combined, these technologies create self-healing and adaptive network behaviors. When AI detects anomalies at edge locations, it automatically adjusts configurations without human intervention. This matters especially for optimizing IoT connectivity in rural areas where manual troubleshooting is impractical.
| Approach | Performance Impact | Adaptability | Resource Efficiency |
|---|---|---|---|
| AI-driven optimization | 25-30% improvement | High, learns patterns | Moderate, requires computing |
| Edge computing | 30% latency reduction | Medium, localized decisions | High, reduces backhaul |
| Traditional methods | Baseline | Low, manual adjustments | Low, centralized processing |
Pro Tip: Prioritize AI tools with proven self-healing capabilities for dynamic network environments. Look for solutions that provide transparency into automated decisions so you can audit and refine optimization rules. Implementing these techniques alongside enterprise WiFi optimization creates comprehensive connectivity improvements.
Security considerations in network optimization
Zero-trust security frameworks assume no implicit trust and verify every connection, making them ideal for distributed cloud and IoT environments. Traditional perimeter security fails when users, devices, and applications exist everywhere. Zero-trust validates identity, device posture, and context for every access request regardless of network location.
SASE architectures consolidate networking and security services, providing seamless enforcement at network edges. Instead of backhauling traffic to centralized security appliances, SASE delivers protection wherever users and devices connect. This reduces latency while maintaining robust security policies across cloud applications and IoT deployments.
Embedding security controls early during optimization reduces vulnerabilities and compliance risks:
- Encryption becomes native to network flows rather than an afterthought
- Microsegmentation limits lateral movement if attackers breach one segment
- Continuous authentication verifies devices and users throughout sessions
- Automated threat response contains incidents before they spread
Quantifiable impacts include 45% vulnerability reduction and 50% fewer security incidents when security integrates with optimization from the start. Organizations implementing IoT security for enterprises alongside network improvements see faster ROI and fewer disruptions.
Pro Tip: Integrate continuous security monitoring alongside performance metrics for holistic optimization. Use unified dashboards displaying bandwidth utilization, latency, and security events together so you can spot correlations between performance and threats. Learn more about network optimization frameworks with security to implement comprehensive protection.
Techniques for IoT network optimization
Resource constraints in IoT require specialized optimization approaches distinct from general networks. IoT devices often have limited processing power, memory, and battery life. Traditional optimization techniques designed for servers and workstations don’t translate effectively to constrained environments.
Granular computing enables fine-grained resource allocation, improving throughput and reducing errors. This approach divides network resources into smaller, manageable units that can be allocated precisely based on device capabilities and application requirements. Granular computing frameworks boost IoT throughput by 25%, reduce energy consumption by 20%, and cut error rates by 60%.
Managing heterogenous IoT devices demands adaptive protocols and localized data processing. Your network likely includes sensors from multiple manufacturers, each with different communication standards and capabilities. Optimization must accommodate this diversity without forcing expensive hardware replacements.
- Assess device capabilities by cataloging processing power, battery life, and communication protocols across your IoT fleet.
- Implement adaptive protocols that automatically adjust data transmission rates based on device constraints and network conditions.
- Deploy edge processing to handle data aggregation and filtering near devices, as demonstrated in optimizing IoT connectivity in rural areas.
- Optimize power management through scheduled communications and sleep modes that extend battery life without sacrificing critical monitoring.
- Monitor device health continuously to predict failures and optimize maintenance schedules before disruptions occur.
Tailored connectivity through wireless internet options for enterprises and mobile internet solutions extends device lifetimes and enhances reliability. Explore granular computing in IoT optimization for deeper technical implementations.
Cloud network optimization strategies
Analyzing and fine-tuning network traffic flows improves throughput and reduces bottlenecks in cloud environments. Traffic engineering identifies congestion points where multiple applications compete for bandwidth. By prioritizing business-critical flows and implementing quality of service policies, you ensure essential applications receive necessary resources.
Strategic resource allocation balances performance needs with cost constraints, avoiding overprovisioning. Cloud providers charge based on data transfer and resource utilization. Optimizing cloud network flows can reduce costs by up to 15% while improving security and performance through efficient resource usage.
Security considerations must align with multi-cloud complexity and hybrid connectivity scenarios. As workloads span AWS, Azure, Google Cloud, and on-premises infrastructure, consistent security policies become challenging. Network optimization includes unified security enforcement across all cloud environments.
Key strategic tactics for optimizing cloud networks:
- Implement SD-WAN to dynamically route traffic across multiple cloud providers based on performance and cost
- Use cloud-native security groups and network policies that move with workloads
- Deploy caching and content delivery networks to reduce redundant data transfers
- Monitor cross-cloud traffic patterns to identify opportunities for consolidation
- Automate scaling policies that adjust resources based on actual demand
Continuous monitoring through cloud networking SMB connectivity and security ensures networks adapt to evolving business needs and threat landscapes. Leverage comprehensive cloud network optimization guides to refine your implementation.
Conceptual framework for network optimization in cloud and IoT
An integrated framework combining AI-enabled traffic and resource management, edge computing for local processing, and zero-trust security models creates resilient and scalable networks. Rather than treating these components as separate initiatives, successful optimization weaves them together into a cohesive architecture.
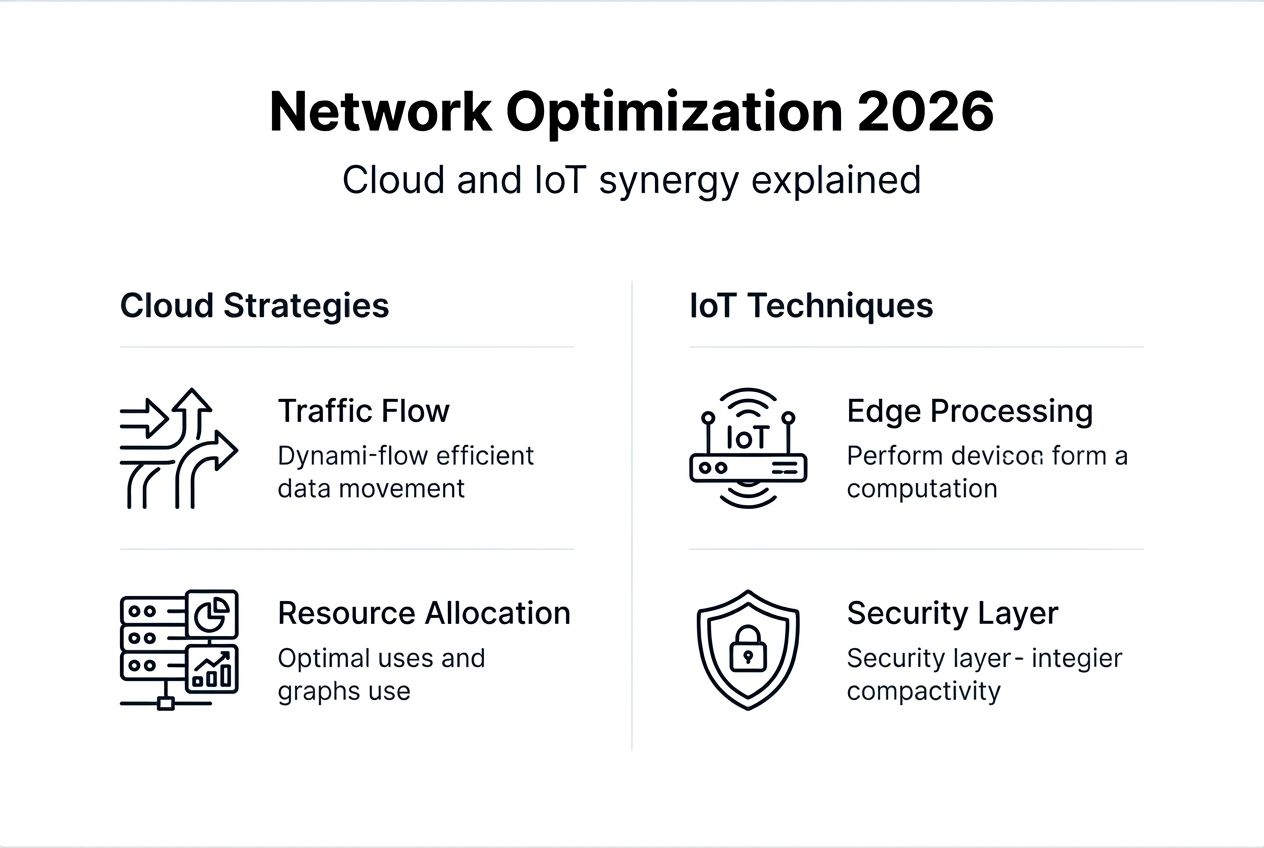
Framework components work synergistically. AI analyzes traffic patterns across edge nodes and cloud environments, making intelligent routing decisions. Edge computing reduces load on centralized systems while providing low-latency processing for time-sensitive IoT applications. Zero-trust security validates every connection regardless of where it originates, protecting data as it moves between edge, cloud, and on-premises systems.
| Approach | Performance Gain | Adaptability | Security Posture |
|---|---|---|---|
| Integrated framework | 35% improvement | High, self-optimizing | Strong, embedded protection |
| AI only | 25% improvement | Medium, traffic-focused | Weak, separate controls |
| Traditional | Baseline | Low, manual | Moderate, perimeter-based |
Integrated frameworks combining AI, edge computing, and zero-trust improve operational metrics by 35% versus isolated solutions. This comprehensive approach delivers greater value than the sum of individual optimizations.
“The future of network optimization isn’t choosing between performance, security, or cost efficiency. It’s building intelligent architectures that deliver all three simultaneously through integrated frameworks.”
Embedding security and intelligent processing at the edge creates networks that heal themselves, adapt to changing conditions, and protect assets without constant manual intervention. This model serves as a blueprint for mid-sized enterprises seeking holistic network optimization that scales with business growth.
Implementing network optimization: practical steps for mid-sized enterprises
Transform your network through a structured implementation sequence that builds capabilities progressively while minimizing disruption.
-
Assess current network infrastructure by mapping all devices, connections, and traffic flows. Establish baseline measurements for latency, throughput, packet loss, and security incidents. Identify bottlenecks where performance degrades and vulnerabilities where security gaps exist. This foundation informs all subsequent optimization decisions.
-
Implement AI-driven traffic management and predictive maintenance tools to enhance adaptability. Start with monitoring and alerting before enabling automated remediation. Validate that AI recommendations align with business priorities before granting full autonomy. Gradually expand automation as confidence grows.
-
Deploy edge computing solutions for localized data processing in IoT environments. Begin with non-critical applications to test edge capabilities and refine configurations. Move mission-critical workloads to edge infrastructure once you’ve proven reliability and performance gains.
-
Embed zero-trust security frameworks ensuring protection throughout optimization, as detailed in IoT security for enterprises. Implement microsegmentation to contain potential breaches. Require continuous authentication for all connections. Integrate security monitoring with performance dashboards.
-
Continuously monitor performance and security metrics and iterate improvements accordingly. Network optimization isn’t a one-time project but an ongoing process. Review metrics weekly, analyze trends monthly, and adjust strategies quarterly based on business evolution and technology advances. Align with cloud networking connectivity and security best practices.
Pro Tip: Customize solutions to your specific enterprise size, device profile, and traffic demands to avoid common pitfalls. Don’t implement every advanced feature immediately. Prioritize optimizations delivering the greatest impact for your unique environment and build complexity gradually as capabilities mature.
Optimize your enterprise network with expert solutions
Transforming network performance, security, and efficiency requires specialized expertise and proven solutions tailored to mid-sized enterprises. Sabertooth Pro offers comprehensive IT and IoT solutions that integrate AI-driven optimization, edge computing capabilities, and embedded security frameworks designed specifically for cloud and IoT environments.
Our IoT solutions leverage the advanced techniques covered in this guide, delivering measurable improvements in latency, throughput, and cost efficiency. We combine next-gen firewalls, zero-trust architectures, and intelligent connectivity through our wireless internet provider services to create resilient networks that scale with your business.
Partner with providers experienced in tailored network optimization to maximize ROI and minimize implementation risks. Our team helps mid-sized enterprises navigate the complexity of modern cloud and IoT networks, translating technical capabilities into business outcomes that drive growth and competitive advantage.
Frequently asked questions
What is the primary benefit of network optimization for mid-sized enterprises?
Network optimization improves connectivity, security, and cost efficiency simultaneously, enabling scalable and resilient operations that support business growth. Rather than addressing these concerns separately, integrated optimization delivers synergistic benefits that compound over time.
How does AI improve network optimization in cloud and IoT environments?
AI enables real-time traffic prediction and automated configuration, reducing latency and boosting throughput. Machine learning algorithms analyze patterns humans can’t detect at scale, making intelligent routing decisions that adapt to changing conditions without manual intervention.
Why is embedding security important during network optimization rather than after?
Integrating security frameworks like zero-trust reduces vulnerabilities and compliance risks more effectively than bolted-on controls. Security built into the network architecture from the start protects data flows inherently rather than relying on perimeter defenses that attackers bypass. This approach prevents costly retrofits and eliminates security gaps that exist between optimization and protection layers.
How long does network optimization implementation typically take for mid-sized enterprises?
Implementation timelines vary based on network complexity and existing infrastructure, but most mid-sized enterprises see initial improvements within 3-6 months and achieve full optimization maturity within 12-18 months. Phased approaches deliver incremental value throughout the process rather than requiring complete transformation before realizing benefits.
