Essential features of business routers for SMBs in 2026
Selecting the right business router is critical for small and medium enterprises facing escalating cyber threats and demanding performance requirements. Your network infrastructure forms the foundation of security, productivity, and operational continuity. With over 90% of breaches starting from misconfigured or outdated firewalls, understanding essential router features becomes non-negotiable. This guide walks you through the evaluation criteria, security technologies, connectivity innovations, and practical comparisons to empower your purchasing decision. You’ll discover how modern routers integrate advanced security, SD-WAN capabilities, and unified management to protect your business while optimizing network performance.
Table of Contents
- Criteria For Evaluating Business Routers
- Advanced Security Features In Business Routers
- SD-WAN And Connectivity Management For SMBs
- Comparing Top Business Router Models For SMBs
- Explore Reliable Business Internet Solutions With Sabertooth Pro
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Security integration | Modern business routers must include stateful firewalls, intrusion prevention systems, and deep packet inspection to prevent breaches effectively. |
| SD-WAN advantages | Software-defined networking provides policy-driven routing, automatic failover, and load balancing that traditional routers cannot match. |
| Unified management | Cloud-based control interfaces reduce IT overhead and simplify multi-site network administration for growing SMBs. |
| Performance metrics | Evaluate throughput capacity, concurrent session limits, and VPN speeds to ensure routers handle your actual workload demands. |
| Scalability matters | Choose routers with firmware update support and modular licensing to accommodate business growth without costly replacements. |
Criteria for evaluating business routers
When assessing business routers, you need a structured framework that balances security, performance, connectivity, and manageability. Start with security features as your foundation. Look for stateful firewalls that track connection states, intrusion detection and prevention systems that identify threats in real time, and deep packet inspection capabilities that examine data payloads for malicious content. These features work together to create multiple defense layers against sophisticated attacks.
Network performance metrics determine whether your router can handle daily operations without bottlenecks. Evaluate throughput capacity measured in Gbps, which indicates maximum data transfer rates. Check concurrent session limits to ensure the router supports your user count and application needs. VPN performance matters significantly if you have remote workers or multiple office locations requiring secure tunnels. A router advertising 1 Gbps throughput might only deliver 200 Mbps with VPN encryption enabled, so verify these specifications carefully.

Connectivity features expand your network’s flexibility and resilience. Multi-WAN support allows you to connect multiple internet links for redundancy and load distribution. VLAN capabilities let you segment traffic by department or function, improving security and performance. SD-WAN technology provides intelligent routing across multiple connections, automatically shifting traffic when one link degrades. These features transform basic connectivity into a strategic advantage.
Manageability directly impacts your IT team’s efficiency and operational costs. Unified management interfaces consolidate configuration, monitoring, and troubleshooting into single dashboards. Cloud-based controls enable remote administration without VPN access to each device. License models vary widely, from perpetual purchases to subscription-based services. Evaluate total cost of ownership over three to five years, not just initial hardware prices.
Reliability features ensure business continuity when problems occur. Hardware redundancy options like dual power supplies prevent single points of failure. Automatic failover capabilities switch traffic to backup connections within seconds. Firmware update support from manufacturers keeps your devices protected against emerging threats. For SMBs, the winning firewall balances accessibility, scalability, and affordability without sacrificing essential protections.
Pro Tip: Create a weighted scoring matrix with these criteria before evaluating specific models. Assign importance values based on your business priorities, then score each router objectively. This approach prevents feature overload and keeps you focused on what truly matters for your environment.
Advanced security features in business routers
Next-generation firewalls represent the current standard for business router security, integrating multiple protection technologies into unified platforms. These systems combine traditional stateful inspection with application-level controls, VPN services, intrusion prevention, and content filtering. Instead of managing separate security appliances, you get comprehensive protection through a single device. This integration reduces complexity while improving threat visibility across your network perimeter.
AI-driven threat detection elevates security beyond signature-based approaches. Machine learning algorithms analyze traffic patterns to identify anomalies that indicate zero-day exploits or advanced persistent threats. Zero Trust Network Access frameworks verify every connection attempt regardless of source location, eliminating the concept of trusted internal networks. SASE architectures merge network and security functions into cloud-delivered services, particularly valuable for organizations with distributed workforces or multiple branch offices.
The business impact of robust security measures proves substantial. Organizations with comprehensive security experienced 60% fewer successful cyberattacks compared to those relying on basic protections. This reduction translates directly into lower incident response costs, reduced downtime, and preserved customer trust. For SMBs without dedicated security teams, router-integrated protections provide enterprise-grade defenses without requiring specialized expertise.
Outdated firewall configurations create dangerous vulnerabilities that attackers actively exploit. Default credentials, disabled security features, and missing patches leave networks exposed to automated scanning tools. Regular firmware updates address newly discovered vulnerabilities and improve detection capabilities. Establish update schedules during maintenance windows, test configurations in staging environments when possible, and maintain rollback procedures for problematic updates.
Key security features to prioritize include:
- Stateful packet inspection tracking connection context and blocking suspicious patterns
- SSL/TLS decryption revealing threats hidden in encrypted traffic streams
- Geo-blocking capabilities restricting connections from high-risk countries
- Application control limiting bandwidth-intensive or risky software usage
- Sandboxing technology detonating suspicious files in isolated environments
Security isn’t a checkbox feature, it’s an ongoing operational discipline. The most advanced firewall becomes useless without proper configuration, regular updates, and active monitoring.
Your security posture depends equally on technology and process. Securing remote networks requires coordinated policies across devices, users, and applications. Additional security insights help you understand evolving threat landscapes and adapt defenses accordingly.
SD-WAN and connectivity management for SMBs
SD-WAN technology fundamentally changes how business routers handle multiple internet connections. Traditional routers use static routing tables and manual failover configurations. SD-WAN separates the control layer from the data forwarding plane, enabling centralized policy management and intelligent traffic steering. This architecture allows real-time decisions based on application requirements, link quality, and business priorities rather than simple routing protocols.
Policy-driven routing represents SD-WAN’s core advantage. You define rules based on application type, destination, time of day, or other criteria. The system automatically selects optimal paths for each traffic flow. Video conferencing might route over your fiber connection for low latency, while bulk file transfers use cable internet to preserve premium bandwidth. When link quality degrades, traffic shifts seamlessly without manual intervention or user disruption.
Link redundancy and load balancing maximize your connectivity investments. Instead of keeping backup connections idle until primary links fail, SD-WAN actively uses all available bandwidth. Traffic distributes across connections based on capacity and performance. If one link experiences packet loss or latency spikes, affected applications instantly move to healthier paths. This active-active approach delivers better performance and higher effective bandwidth than traditional active-passive designs.
Real-world implementations demonstrate SD-WAN’s practical benefits. Healthcare clinics using UniFi SD-WAN maintain uninterrupted electronic health record access across multiple sites despite varying internet service quality. When one location’s primary connection fails, patient data flows continue through backup links without affecting clinical workflows. This reliability proves essential for organizations where connectivity directly impacts service delivery.
| Feature | Traditional WAN | SD-WAN |
|---|---|---|
| Failover speed | 30-90 seconds | Under 1 second |
| Link utilization | Single active path | All links active |
| Traffic prioritization | Basic QoS only | Application-aware policies |
| Management complexity | Per-device CLI | Centralized dashboard |
| Deployment time | Days per site | Hours for multiple sites |
Key SD-WAN features for SMB routers include:
- Application identification and classification recognizing thousands of programs automatically
- Dynamic path selection choosing routes based on real-time performance metrics
- Forward error correction compensating for packet loss without retransmission delays
- WAN optimization compressing data and caching frequently accessed content
- Zero-touch provisioning simplifying remote site deployments through cloud orchestration
Pro Tip: Start with basic SD-WAN policies focused on business-critical applications before implementing complex rules. Monitor traffic patterns for two weeks to understand actual usage, then refine policies based on observed behavior rather than assumptions.
Understanding the differences between SD-WAN and traditional approaches helps you evaluate whether this technology fits your needs. Cloud-based SD-WAN management offers particular advantages for multi-site organizations or those with limited IT resources.
Comparing top business router models for SMBs
FortiGate models dominate SMB deployments due to their balance of performance, security features, and pricing. The 30G entry model handles networks up to 50 users with 5 Gbps firewall throughput and 1.5 Gbps IPsec VPN capacity. The 40F mid-range option scales to 100 users, delivering 10 Gbps firewall throughput and 2 Gbps VPN performance. The 80F enterprise model supports 250+ users with 20 Gbps firewall capacity and 6 Gbps VPN speeds. These detailed specifications help match hardware to actual workload demands.
| Model | Firewall Throughput | VPN Throughput | Concurrent Sessions | Typical User Count | Starting Price |
|---|---|---|---|---|---|
| FortiGate 30G | 5 Gbps | 1.5 Gbps | 250,000 | 25-50 | $600 |
| FortiGate 40F | 10 Gbps | 2 Gbps | 500,000 | 50-100 | $1,200 |
| FortiGate 80F | 20 Gbps | 6 Gbps | 1,000,000 | 100-250 | $2,800 |
| Cisco Meraki MX67 | 450 Mbps | 200 Mbps | 100,000 | 25-50 | $1,000 + licensing |
| Ubiquiti Dream Machine Pro | 3.5 Gbps | 1 Gbps | 200,000 | 25-75 | $380 |
Security features vary significantly across models despite similar throughput ratings. FortiGate devices include comprehensive threat intelligence feeds, SSL inspection, and advanced malware protection in base licenses. Cisco Meraki requires ongoing subscriptions for security services, increasing total cost but providing automatic updates and simplified management. Ubiquiti offers strong basic security but lacks some enterprise features like sandboxing or advanced threat prevention found in higher-tier products.
Performance under real-world conditions often differs from marketing specifications. Maximum throughput numbers assume ideal traffic without security inspection enabled. Activate IPS, antivirus scanning, and SSL decryption, and effective throughput typically drops 40-60%. Size your router based on expected performance with all security features active, not theoretical maximums. If you need 1 Gbps actual throughput with full security, choose a model rated for 2-3 Gbps baseline capacity.
Cost versus performance tradeoffs require careful analysis beyond initial hardware prices. Consider these factors:
- Annual licensing fees for security subscriptions, support contracts, and cloud management
- Replacement cycles based on vendor support timelines and performance headroom
- Management time savings from unified interfaces versus per-device configuration
- Scalability costs when adding sites, users, or bandwidth capacity
Pro Tip: Request evaluation units or proof-of-concept deployments before committing to specific models. Test with your actual traffic patterns, security policies, and management workflows. Vendor specifications tell you what’s possible, but hands-on testing reveals what’s practical for your environment.
Business-grade internet connectivity complements router capabilities, ensuring your hardware investment delivers expected performance. Match router specifications to your internet service speeds and quality requirements for optimal results.
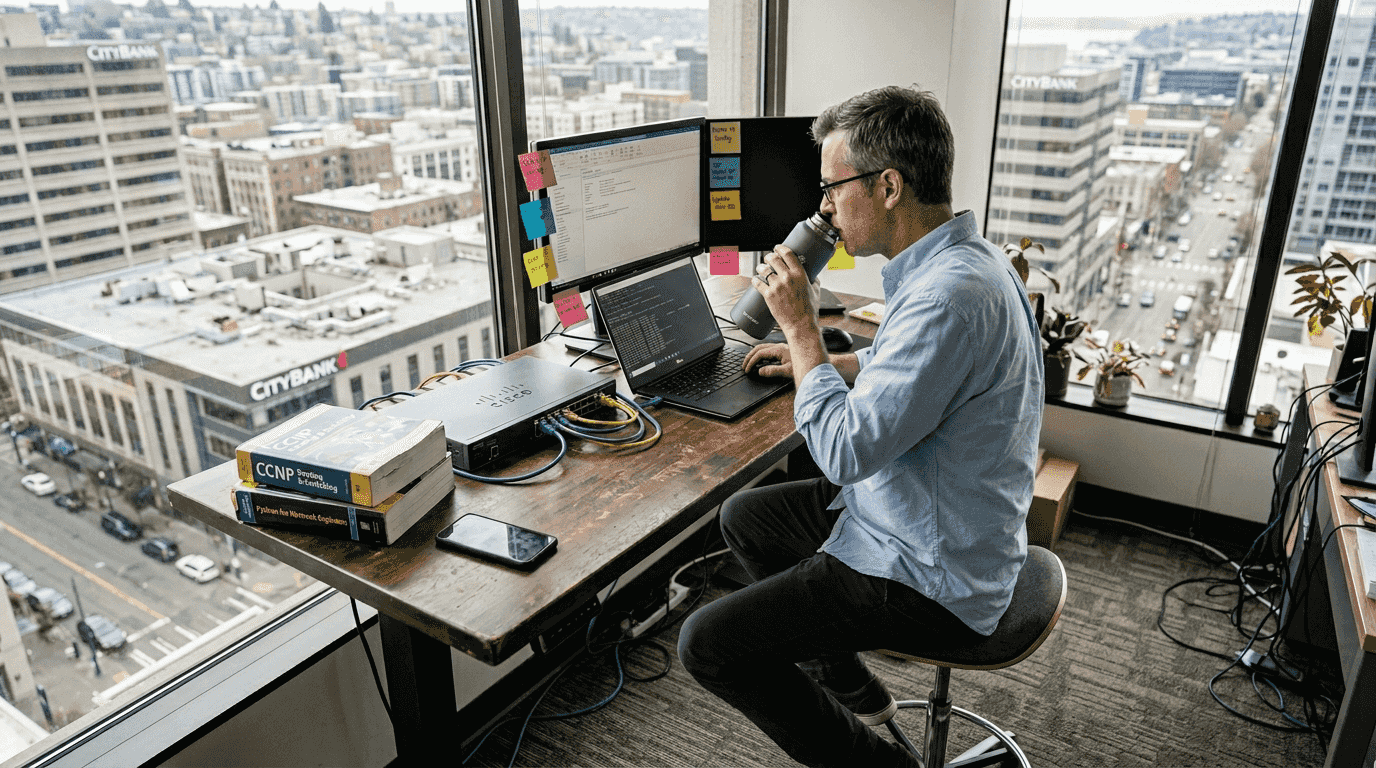
Explore reliable business internet solutions with Sabertooth Pro
Selecting the right router represents just one piece of your network infrastructure puzzle. You need reliable, high-performance internet connectivity that matches your hardware capabilities and business demands. Sabertooth Pro delivers scalable wireless internet solutions designed specifically for SMB networking requirements. Our plans provide the bandwidth, uptime, and support necessary to maximize your router investment.
Our wireless internet services eliminate the limitations of traditional wired connections, offering flexible deployment options for primary connectivity or automatic failover backup. Advanced IoT integration capabilities extend your network to connected devices, sensors, and remote monitoring systems that enhance operational efficiency. The 5G Bolt wireless device delivers enterprise-grade 5G speeds with the reliability your business applications demand.
Our expert team helps you design, implement, and optimize complete network solutions that align technology choices with business objectives. We understand the challenges SMBs face balancing security, performance, and budget constraints. Let us guide you toward connectivity infrastructure that grows with your organization.
Frequently asked questions
What security features are essential in business routers?
Essential security features include stateful firewalls tracking connection states, intrusion prevention systems detecting threats in real time, and deep packet inspection examining data payloads. VPN capabilities for secure remote access and regular firmware updates addressing vulnerabilities are equally critical for protecting SMB networks.
How does SD-WAN improve business connectivity?
SD-WAN intelligently routes traffic across multiple internet connections based on application requirements and real-time link quality. It provides automatic failover within seconds, optimizes bandwidth usage across all connections simultaneously, and simplifies management through centralized policy control rather than per-device configuration.
What throughput capacity does my business actually need?
Calculate throughput by adding your internet connection speeds, then multiply by 1.5-2x to account for security processing overhead and growth. A business with 500 Mbps internet should choose routers rated for 1-1.5 Gbps firewall throughput with security features enabled, not disabled baseline specs.
Why do firmware updates matter for business routers?
Firmware updates patch security vulnerabilities that attackers actively exploit, improve threat detection capabilities, and enhance performance or add features. Manufacturers discover and fix dozens of vulnerabilities annually. Without regular updates, your router becomes increasingly vulnerable regardless of its initial security features.
How do I choose between subscription and perpetual licensing?
Subscription licensing provides ongoing security updates, support access, and cloud management features with predictable annual costs. Perpetual licenses require larger upfront investments but lower ongoing expenses. Choose subscriptions if you need latest threat intelligence and prefer operational expense budgeting, perpetual if you have capital budget and internal security expertise.
What router features support business growth?
Look for modular port expansion, stackable designs adding capacity without replacing core devices, and licensing models allowing feature upgrades without hardware changes. Cloud-based management scales easily across multiple sites. Choose routers from manufacturers with clear product roadmaps and multi-year support commitments to protect your investment.
