Network Security for Enterprises: Reducing Risk in 2026

Cyber threats are never far from your network. For IT leaders across the Mid-Atlantic, the challenge is about more than stopping the latest malware—it means creating a defense that combines strong technical controls, robust policies, and vigilant physical protection. With attackers constantly probing for weaknesses, staying current on layered security controls and adaptive frameworks helps safeguard your organization’s reputation and regulatory standing while supporting business operations.
Table of Contents
- Defining Network Security For Modern Enterprises
- Key Security Models And Core Technologies
- Zero Trust, Sase, And Ai Trends In Security
- Regulatory Compliance And Accountability In 2026
- Managed Security Services And Avoiding Common Pitfalls
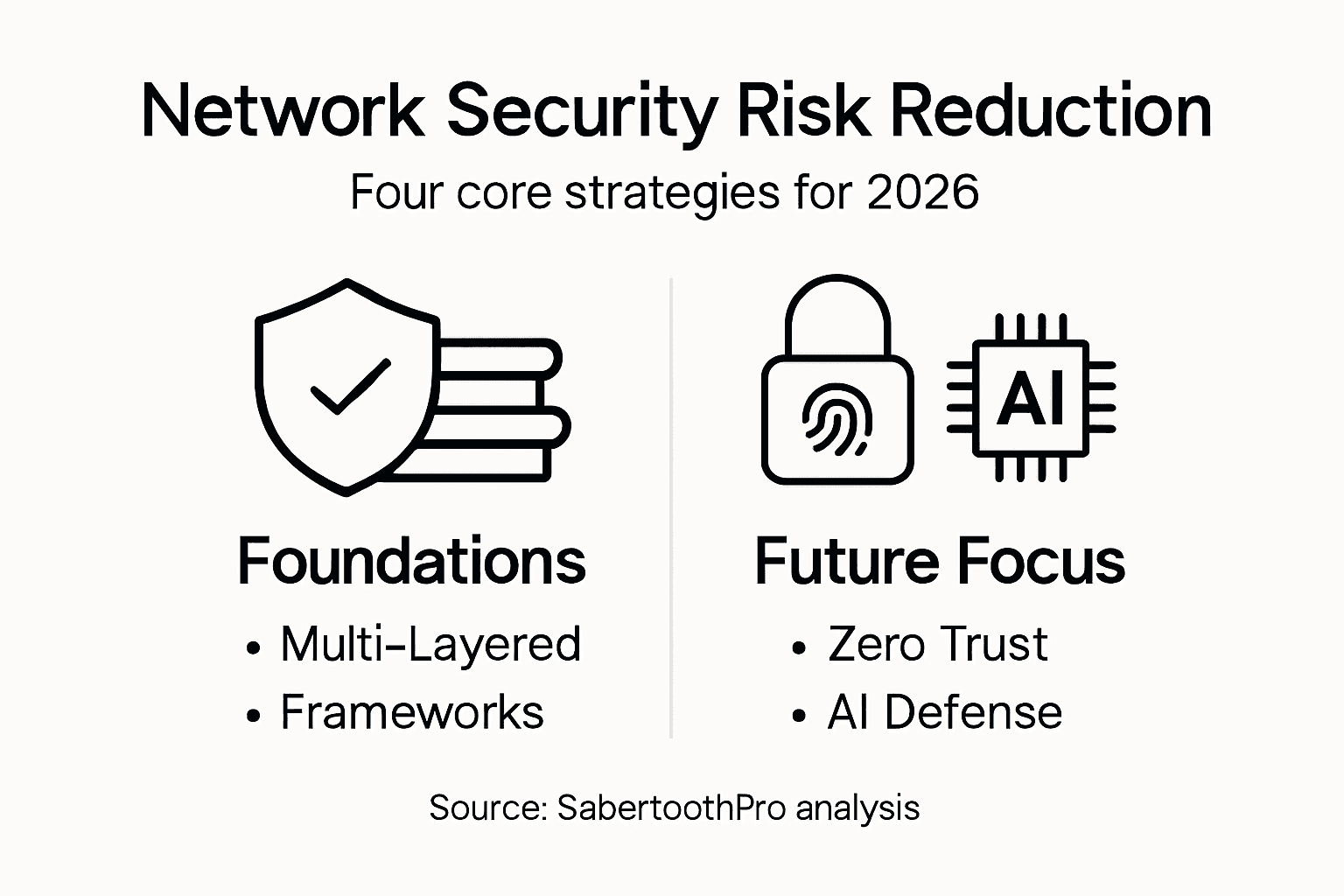
Key Takeaways
| Point | Details |
|---|---|
| Multi-Layered Security | Effective network security integrates physical, technical, and administrative controls to protect against cyber threats. |
| Adoption of Zero Trust | Transition to Zero Trust principles requires continuous verification of all users and devices, reducing attack vulnerability. |
| Utilization of Advanced Technologies | Incorporate AI-driven detection systems and continuous monitoring to enhance threat identification and response times. |
| Regulatory Compliance | Maintain accountability and documentation to ensure adherence to industry-specific security regulations, avoiding legal repercussions. |
Defining Network Security for Modern Enterprises
Network security for modern enterprises means protecting your organization’s data, systems, and infrastructure from unauthorized access, theft, and cyberattacks. It’s not just about having a firewall—it’s a multi-layered approach that covers physical hardware, software controls, and organizational policies working together.
Your network faces constant threats today. Attackers target businesses of all sizes, looking for vulnerabilities to exploit for financial gain, data theft, or operational disruption. The damage from a successful breach goes beyond immediate costs—it damages reputation, erodes customer trust, and creates regulatory complications.
The Three Pillars of Network Security
Effective network security rests on three essential components:
-
Physical security: Protecting the actual hardware—servers, routers, cables, and data center infrastructure from theft or damage.
-
Technical security: Implementing software-based controls like firewalls, encryption, intrusion detection systems, and access controls that monitor and block threats.
-
Administrative security: Creating and enforcing policies, procedures, and training programs that guide how employees handle data and systems.
Each pillar is equally critical. Skip one, and your security framework has a dangerous gap.
Why This Matters for Mid-Atlantic Enterprises
Your organization likely processes sensitive customer data, financial records, and proprietary information. A security failure puts all of it at risk. Beyond the immediate consequences, regulatory bodies in your region enforce compliance requirements that demand specific security measures.
Modern enterprise security isn’t about achieving perfect protection—it’s about managing risk through layered defenses that make breaches expensive and difficult for attackers.
Building on Established Frameworks
You don’t need to build your security strategy from scratch. The NIST Cybersecurity Framework provides comprehensive guidance for managing cybersecurity risks without dictating specific tools or technologies. It helps you understand, assess, prioritize, and communicate your security efforts across your organization.
A layered security approach protects against common threats like phishing attacks, malware infiltration, and unauthorized access. Network segmentation separates critical systems from general networks, limiting damage if one area is compromised.
When implementing secure internet connectivity for enterprise operations, you create the foundation for every other security measure. Poor connectivity choices undermine everything else you build.
Pro tip: Start by documenting what data your organization actually has, where it lives, and who needs access to it. This inventory becomes the foundation for every security decision you make.
Key Security Models and Core Technologies
Modern enterprise security relies on proven foundational models combined with cutting-edge technology. Your security posture depends on understanding both—the frameworks that guide decisions and the tools that enforce them.

The security models you choose shape how threats are detected, responded to, and prevented. Without the right technologies backing them up, even the best model fails. Together, they create a defense system that adapts to new threats while maintaining operational efficiency.
Foundational Security Technologies
Every enterprise network needs core defensive tools:
-
Firewalls: Control incoming and outgoing traffic, blocking unauthorized access before it enters your network.
-
Network address translation: Masks internal IP addresses, adding a layer of anonymity that complicates attacker reconnaissance.
-
Encryption protocols: Scramble data in transit so even if intercepted, information remains unreadable.
-
Denial-of-service mitigation: Absorbs and neutralizes traffic floods designed to crash your systems.
These foundational technologies have proven effective for decades. They remain essential because attackers still use the same basic methods they always have.
Here is a quick comparison of foundational and advanced network security technologies and their impacts on enterprises:
| Technology Type | Main Example | Business Benefit |
|---|---|---|
| Foundational | Firewall | Prevents unauthorized network access |
| Foundational | Network Address Translation | Masks internal addresses to protect assets |
| Foundational | Encryption | Keeps data private in transit |
| Advanced | Intrusion Detection System | Alerts immediately to suspicious activity |
| Advanced | Continuous Monitoring | Finds unusual behavior quickly |
| Advanced | Secure DNS | Stops connections to malicious domains |
Advanced Detection and Response
Foundational tools aren’t enough anymore. Your enterprise also needs:
-
Intrusion detection systems: Monitor network traffic for suspicious patterns and alert security teams in real time.
-
Secure DNS: Blocks access to malicious domains before connections establish.
-
Continuous monitoring: Tracks system behavior 24/7, catching anomalies humans might miss.
-
Adaptive security frameworks: Automatically adjust defenses based on current threat levels and network conditions.
These advanced capabilities help you detect breaches faster, reducing the damage window from months to hours.
Artificial Intelligence in Enterprise Security
AI-enhanced detection systems are reshaping how enterprises defend themselves. Machine learning algorithms identify threats that traditional signature-based detection would miss. They process massive datasets instantly, spotting patterns humans never could.
However, AI introduces new risks. Attackers use AI-powered tools to craft more sophisticated attacks. Your security strategy must balance automation with human oversight—machines spot threats faster, but humans make decisions.
The most effective security models in 2026 combine AI-powered detection with human judgment, creating resilience against both current and evolving threats.
Building Your Technology Stack
Your organization doesn’t need every technology available. Focus on technologies that address your specific threats and integrate with existing systems. When devices like IoT endpoints are connected to your network, IoT security considerations become critical to your overall defense strategy.
Technology choices should align with regulatory requirements in your region and your industry vertical. Retail operations face different threats than healthcare providers.
Pro tip: Prioritize technologies that provide visibility into your network first—you can’t defend what you can’t see. Detection capabilities should come before investing in advanced response automation.
Zero Trust, SASE, and AI Trends in Security
Three major shifts are reshaping enterprise security in 2026. Zero Trust architecture eliminates the assumption that anyone inside your network is automatically trustworthy. SASE delivers security and networking through cloud infrastructure. AI transforms how threats are detected and stopped. Understanding these trends isn’t optional—they’re becoming industry standards.
Your enterprise likely still operates with perimeter-based security, trusting users and devices once they’re inside the firewall. That model is dead. Modern threats come from everywhere—compromised employee devices, insider threats, and supply chain infiltration. You need continuous verification, not one-time authentication.
Understanding Zero Trust
Zero Trust architecture shifts from trusting based on location to verifying every access request. The core principle: never trust, always verify.
Zero Trust implementation requires:
-
Minimizing implicit trust: Stop assuming internal users are safe. Treat all access requests as potentially hostile.
-
Strict authentication: Require multi-factor verification for every system access, regardless of user history.
-
Least privilege access: Users and devices get only the permissions needed for their specific role, nothing more.
-
Continuous verification: Verify identity and device posture constantly, not just at login.
This sounds restrictive, but done right, it barely impacts productivity while eliminating huge attack surfaces.
SASE: Networking and Security Merged
Secure Access Service Edge combines network security functions with connectivity in a single cloud platform. Instead of routing traffic through corporate data centers, SASE delivers security at the edge—closer to users and devices.
For distributed workforces, this is transformative. Remote employees get secure, fast access without VPN bottlenecks. Branch offices connect securely without backhaul to headquarters.
SASE architecture supports modern work environments where employees operate from anywhere, requiring both flexibility and security simultaneously.
Artificial Intelligence Powering Defense
AI is advancing cyber defense capabilities dramatically. Machine learning models detect anomalies humans would miss, hunt for threats proactively, and respond to incidents faster than security teams can.
AI-powered security includes:
-
Proactive threat hunting: AI systems search your network for indicators of compromise before attacks succeed.
-
Anomaly detection: Machine learning identifies unusual behavior patterns that signal breaches.
-
Automation at scale: Responds to thousands of alerts simultaneously, prioritizing critical threats.
However, balancing automation with human oversight remains critical. AI speeds up detection and response, but humans should make final decisions on sensitive actions.
The following table summarizes key network security trends and the organizational shifts they require:
| Trend | Core Principle | Organizational Shift Needed |
|---|---|---|
| Zero Trust | Verify all access continuously | Apply least privilege and MFA |
| SASE | Security at network edge | Integrate security with connectivity |
| AI | Automated threat detection | Balance automation with human review |
Building Your 2026 Security Roadmap
Starting with Zero Trust, SASE, and AI doesn’t mean ripping out everything you have. Understanding current technology trends and adoption timelines helps you plan realistic implementation phases.
Prioritize Zero Trust principles first, then add SASE connectivity, then layer in AI-driven threat detection. This sequence allows each layer to mature before adding complexity.
Pro tip: Begin your Zero Trust journey by mapping your critical assets and access paths, then apply verification controls where attackers would gain the most value—this focused approach delivers faster wins than trying to secure everything at once.
Regulatory Compliance and Accountability in 2026
Regulatory requirements for network security are tightening. Your Mid-Atlantic enterprise operates under multiple compliance frameworks—HIPAA if you handle healthcare data, PCI DSS for payment processing, state privacy laws, and federal standards. Falling out of compliance costs money, damages reputation, and creates legal liability.
Compliance isn’t about checking boxes. It’s about demonstrating that your organization takes security seriously through continuous risk management, documented policies, and accountability mechanisms.
Understanding Your Regulatory Landscape
Your compliance obligations depend on your industry and the data you handle:
-
Healthcare: HIPAA requires protection of electronic protected health information with specific technical and administrative safeguards.
-
Payment processing: PCI DSS mandates secure handling of credit card data across networks and systems.
-
State privacy laws: California’s CCPA, Virginia’s VCDPA, and similar laws require consent and data protection standards.
-
Critical infrastructure: Certain industries face federal security directives that define minimum security requirements.
Ignoring even one applicable regulation exposes your organization to fines, enforcement actions, and breach notification costs.
Enhanced HIPAA Security Requirements
Healthcare organizations in your region face heightened scrutiny. The proposed HIPAA Security Rule updates require continuous risk analysis, enhanced technical safeguards, and mandatory documentation of security policies.
Key updates include:
-
Continuous risk assessment: No longer acceptable to perform annual reviews. You must assess risks continuously.
-
Enhanced definitions: New technical terms clarify what protections mean in modern environments.
-
Mandatory documentation: Security policies must be written, approved, and maintained with evidence of compliance.
-
Technical safeguards: Systems must implement current encryption standards and access controls reflecting today’s threats.
These changes affect hospitals, clinics, insurance companies, and any healthcare provider handling patient data.
Federal Guidance and Accountability
The Cybersecurity and Infrastructure Security Agency leads national efforts to improve critical infrastructure security. CISA provides guidance, incident response coordination, and enforcement of cybersecurity standards that affect enterprises across sectors.
CISA doesn’t just advise—they coordinate national responses to breaches, investigate compromises of critical systems, and issue directives that organizations must follow. Their information-sharing programs help enterprises understand emerging threats.
Regulatory compliance in 2026 requires demonstrating continuous security improvement, not static adherence to outdated requirements.
Building Accountability into Your Security Program
Compliance demands accountability. Establish clear ownership of security decisions, document your risk management process, and maintain audit trails showing compliance efforts.
Accountability mechanisms include:
-
Written security policies defining roles, responsibilities, and procedures.
-
Risk assessments documenting identified threats and mitigation strategies.
-
Audit logs proving systems detected and responded to security events.
-
Incident response plans showing how your organization handles breaches.
When regulators audit your organization, these documents prove you operate intentionally, not carelessly.
Pro tip: Assign one person as your security accountability owner—someone responsible for maintaining compliance documentation and coordinating with regulators. This single point of accountability prevents compliance responsibilities from falling through cracks.
Managed Security Services and Avoiding Common Pitfalls
Managed Security Services (MSS) can transform your enterprise security posture—if you implement them correctly. Many organizations hire a managed security provider, then expect the vendor to solve all problems while ignoring internal processes. That approach fails. Success requires clear alignment between your organization’s needs and your vendor’s capabilities.
Most MSS engagements stumble for preventable reasons. Understanding common pitfalls before you sign a contract saves money, reduces frustration, and actually improves your security.
Understanding Managed Security Services
Managed Security Services means outsourcing some or all security functions to a specialized vendor. Typical services include:
-
24/7 monitoring: Security operations centers watching your network continuously.
-
Threat detection: Identifying suspicious activity and alerting your team.
-
Incident response: Helping contain and remediate breaches when they occur.
-
Vulnerability management: Scanning systems and prioritizing fixes.
-
Compliance support: Helping maintain regulatory compliance documentation.
MSS works best when it supplements internal security efforts, not replaces them.
Common Pitfalls and How to Avoid Them
Organizations commonly make mistakes like over-relying on vendors without clear communication, underestimating internal security processes, lacking continuous monitoring, and misaligning MSS solutions with enterprise risk profiles. These gaps create coverage holes attackers exploit.
Avoid these pitfalls:
-
Define clear SLAs: Specify response times, detection requirements, and performance metrics in writing.
-
Maintain internal expertise: Your team should understand security fundamentals, not just delegate everything.
-
Review performance regularly: Monthly or quarterly reviews catch problems before they become disasters.
-
Document all agreements: Written contracts prevent misunderstandings about what services cover.
Many organizations also fail to patch systems timely and provide insufficient security training to employees, undermining whatever MSS provides.
Aligning MSS with Your Risk Profile
Before engaging a vendor, map your critical assets and threats. A managed security provider can’t protect what you haven’t identified.
Your risk profile depends on your industry and data sensitivity. A retail company handling payment cards faces different threats than a manufacturer. Your MSS agreement should specifically address your threats, not generic “we monitor everything” promises.
Effective MSS requires comprehensive planning before vendor selection, clear service level agreements, and active collaboration between your internal team and the managed provider.
Ensuring Integrated Security Frameworks
Your MSS provider handles monitoring and incident response. Your internal team owns patching, employee training, and access controls. Both must work together seamlessly.
When incident response capabilities and system update procedures operate independently, gaps appear. Your MSS team detects an attack while your patching process falls behind. Attackers exploit the delay.
Schedule monthly sync meetings between your team and the MSS provider to discuss emerging threats, review incidents, and adjust monitoring rules.
Pro tip: Start with a managed security engagement for monitoring and threat detection—the areas where vendor expertise delivers immediate value—while keeping incident response, patching, and employee training as internal responsibilities until your team gains experience.
Strengthen Your Enterprise Network Security with SabertoothPro
Scaling your network security for 2026 means embracing next-generation controls like zero trust frameworks, continuous monitoring, and AI-powered detection. The complexity of today’s threats calls for more than just traditional protections. SabertoothPro understands your challenges in reducing risk and meeting compliance demands with solutions designed to integrate seamlessly into your infrastructure. From next-gen firewalls and SOC-as-a-Service to advanced IoT security and reliable connectivity options, we offer the essential tools to build a resilient defense tailored to your enterprise needs.
Take control of your network security today by partnering with SabertoothPro. Explore our comprehensive offerings in enterprise security, IoT connectivity, and high-speed internet solutions that keep your critical systems safe and operational 24/7. Don’t wait until vulnerabilities become costly breaches. Visit SabertoothPro.com now and start strengthening your security posture with expert solutions that evolve with the threat landscape.
Frequently Asked Questions
What is network security for enterprises?
Network security for enterprises involves protecting an organization’s data, systems, and infrastructure from unauthorized access and cyberattacks. It includes a multi-layered approach combining physical, technical, and administrative security measures.
Why is network security important for businesses?
Network security is critical for businesses because it safeguards sensitive customer data, financial information, and proprietary data. A security breach can damage reputation, erode customer trust, and lead to regulatory complications.
What are the three pillars of network security?
The three pillars of network security are physical security (protecting hardware and infrastructure), technical security (software controls like firewalls and encryption), and administrative security (policies and training for handling data and systems).
How can organizations implement a Zero Trust architecture?
Organizations can implement Zero Trust architecture by minimizing implicit trust, requiring strict authentication for all access requests, applying the principle of least privilege, and ensuring continuous verification of users and devices throughout their interaction with the network.
