Role of VPN in Business: Secure Remote Access 2026
Nearly half of organizations experienced VPN-related cyberattacks in recent years, exposing critical vulnerabilities in traditional remote access strategies. As remote work becomes permanent, IT leaders must understand how VPNs function, their inherent risks, and modern approaches like Zero Trust that enhance security without sacrificing usability. This guide delivers actionable insights to optimize your VPN infrastructure and protect your business network.
Table of Contents
- Understanding VPNs And Their Business Role
- Security Vulnerabilities And Risks Of Business VPNs
- Operational Challenges And User Experience Issues With VPNs
- Modernizing VPN Security: Zero Trust Integration And Cloud-Native Solutions
- Framework For Selecting And Transitioning VPN Solutions In Business
- Common Misconceptions About VPN Security And Usage
- Conclusion: Balancing Security, Usability, And Future-Proofing Business VPNs
- Explore Sabertooth Pro’s Secure Connectivity Solutions
Key takeaways
| Point | Details |
|---|---|
| VPN vulnerabilities threaten business security | Traditional VPNs face breaches from credential theft, zero-day exploits, and implicit trust models enabling lateral movement. |
| User experience issues reduce productivity | Slow speeds, disconnects, and complex authentication drive 83% user dissatisfaction and risky workarounds. |
| Zero Trust modernizes secure access | Identity-aware controls and continuous verification improve security, scalability, and user experience over legacy VPNs. |
| Strategic frameworks guide VPN transitions | Assessing risks, planning phased deployments, and balancing security with usability enable effective modernization. |
| Cloud-native VPNs dominate enterprise adoption | Scalable, manageable platforms align with digital transformation and reduce operational overhead for IT teams. |
Understanding VPNs and their business role
A Virtual Private Network encrypts internet traffic between remote users and corporate resources, creating secure tunnels over public networks. This technology became essential when 70% of companies adopted VPNs for remote work security, enabling workforce mobility while maintaining data confidentiality.
VPNs serve critical compliance functions for businesses handling sensitive information under regulations like HIPAA and GDPR. Encrypted connections prevent data interception during transmission, protecting customer records, financial data, and intellectual property from unauthorized access. The role of VPN in remote work extends beyond encryption to establishing trusted pathways for distributed teams accessing centralized resources.
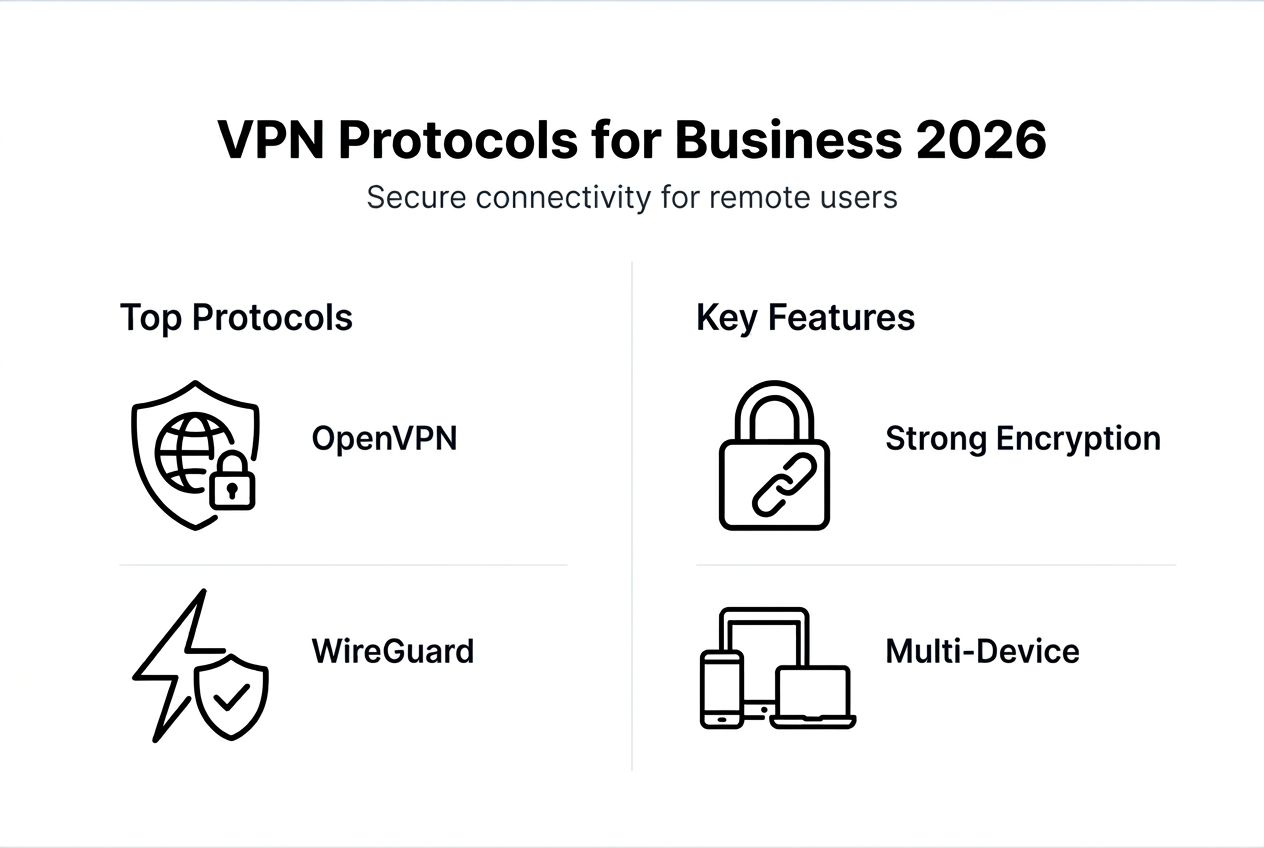
Businesses deploy several VPN protocols based on specific security and performance needs:
- IPSec establishes site-to-site connections between office locations with strong encryption and authentication.
- SSL/TLS VPNs provide browser-based access without dedicated client software, simplifying deployment for remote workers.
- L2TP combined with IPSec delivers enhanced security for mobile users requiring flexible access across devices.
These protocols enable secure internet for enterprise environments while supporting diverse connectivity scenarios from individual remote employees to interconnected branch offices. Understanding remote connectivity key technologies helps IT teams architect appropriate solutions matching organizational security requirements and operational complexity.
Despite widespread adoption, traditional VPN architectures face mounting challenges from evolving cyber threats and changing workforce expectations. The foundation that made VPNs indispensable now reveals cracks requiring immediate attention from security-conscious organizations.
Security vulnerabilities and risks of business VPNs
Enterprise VPNs present attractive targets for attackers seeking network access. Research shows 48% of organizations experienced VPN-related cyberattacks, with 30% suffering multiple incidents highlighting persistent exposure risks threatening business continuity.
Attackers exploit VPN systems through three primary vectors:
- Stolen credentials from phishing campaigns or password reuse grant authenticated access bypassing perimeter defenses.
- Zero-day vulnerabilities in VPN software provide entry points before patches become available or get deployed.
- Misconfigurations like weak encryption settings or excessive user permissions expand attack surfaces unnecessarily.
The implicit trust model embedded in traditional VPN architecture amplifies breach consequences. Once authenticated, users typically gain broad network access based on their credentials alone. This design enables attackers who compromise legitimate accounts to move laterally across systems, escalating privileges and exfiltrating data before detection occurs.
“Traditional VPNs operate on a castle-and-moat security model where authenticated users receive trusted access, but modern threats demand continuous verification regardless of initial authentication.”
Multiple incidents within affected organizations indicate systematic weaknesses rather than isolated events. Attackers establish persistence mechanisms, return through compromised credentials, and exploit the same vulnerabilities across different entry points. This pattern demonstrates how legacy VPN trust assumptions fail against determined adversaries employing sophisticated techniques.
Network security best practices 2026 emphasize defense in depth strategies that complement VPN encryption with additional controls. Implementing multifactor authentication, network segmentation, and behavioral monitoring reduces breach risks even when perimeter defenses face compromise. Organizations relying solely on VPN authentication expose themselves to catastrophic losses from credential theft or software vulnerabilities.
The frequency and severity of VPN-targeted attacks demand immediate reassessment of secure access strategies. IT leaders must evaluate whether current architectures adequately protect against modern threats or require fundamental redesign incorporating contemporary security principles.
Operational challenges and user experience issues with VPNs
Managing VPN infrastructure creates significant operational burdens for IT teams. Statistics reveal 72% of organizations operate multiple VPN services, each requiring separate configuration, monitoring, and maintenance. This fragmentation complicates security policy enforcement across platforms and multiplies potential misconfiguration risks.
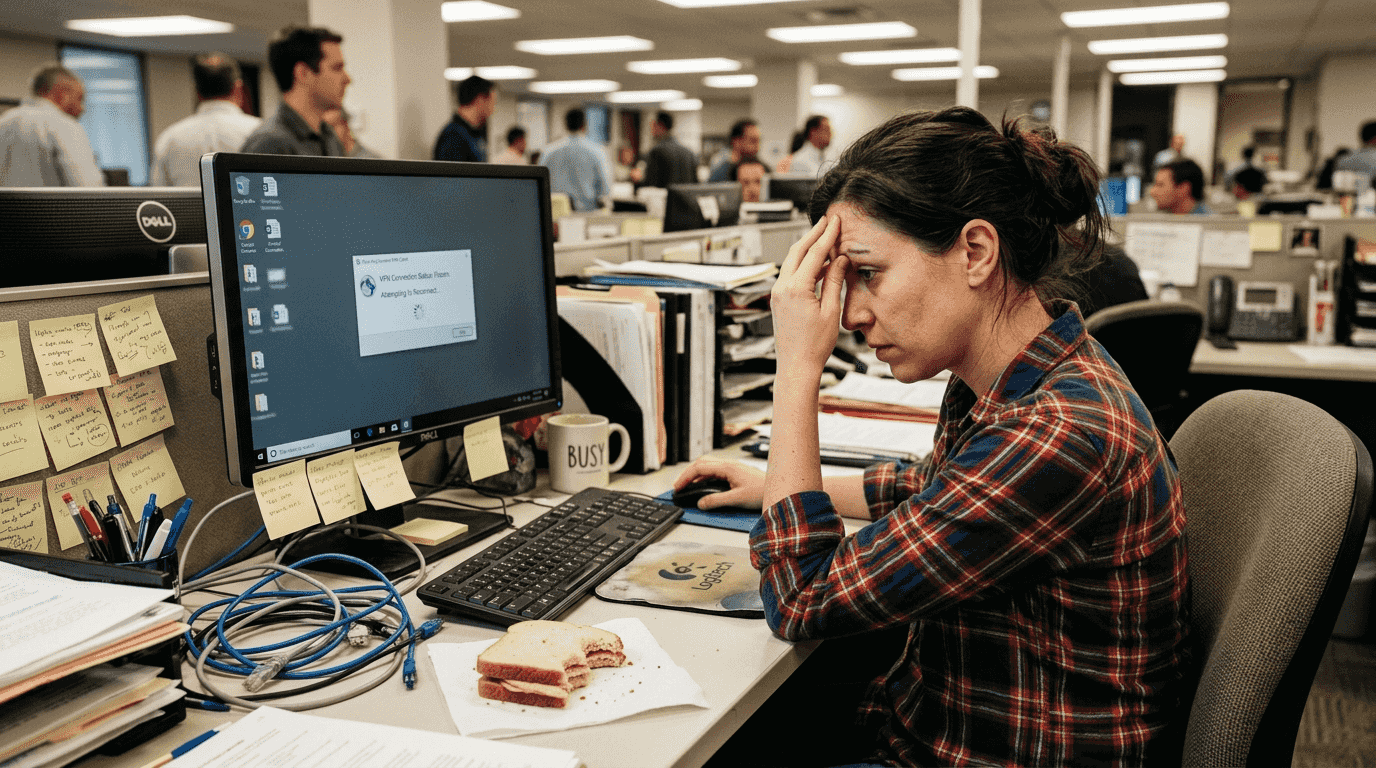
Multiple global gateways intended to improve performance paradoxically increase complexity. IT staff must coordinate updates, manage capacity across regions, and troubleshoot connectivity issues spanning different infrastructure components. Policy inconsistencies between VPN services create security gaps where users exploit the least restrictive path to access resources.
User dissatisfaction with VPN performance directly impacts productivity and security posture. Common complaints include:
- Slow connection speeds degrading application responsiveness and file transfer times.
- Frequent disconnections interrupting workflows and requiring repeated authentication.
- Cumbersome multi-step authentication processes delaying urgent access to critical systems.
These frustrations drive employees toward dangerous workarounds. Workers disable VPNs when accessing less sensitive systems, use personal devices outside corporate controls, or share credentials to bypass authentication friction. Each workaround undermines security investments and expands the attack surface IT teams must defend.
Operational overhead extends beyond infrastructure management to user support. Help desk tickets spike around VPN connectivity problems, consuming resources better allocated to strategic initiatives. Inconsistent experiences across VPN for rural users explained scenarios versus urban deployments create additional support complexity requiring specialized troubleshooting knowledge.
Pro Tip: Monitor user experience metrics like connection success rates, authentication completion times, and support ticket volumes to identify VPN performance issues before they drive risky workarounds that compromise security.
The operational reality of managing legacy VPN infrastructure conflicts with modern expectations for seamless, secure access. Organizations trapped in this complexity cycle struggle to maintain security while delivering the user experience knowledge workers demand. Breaking this cycle requires rethinking secure access architecture from first principles rather than incrementally patching existing systems.
Modernizing VPN security: zero trust integration and cloud-native solutions
Zero Trust Network Access fundamentally reimagines secure connectivity by eliminating implicit trust assumptions. Rather than granting broad access after initial authentication, ZTNA enforces continuous verification of user identity, device posture, and contextual factors throughout each session. This paradigm shift directly addresses the lateral movement risks plaguing traditional VPNs.
| Capability | Traditional VPN | Zero Trust Network Access |
|---|---|---|
| Access model | Broad network access post-authentication | Least privilege per-application access |
| Trust assumption | Implicit trust inside perimeter | Continuous verification required |
| User experience | Complex client setup, connection delays | Seamless application access |
| Scalability | Hardware capacity constraints | Cloud-elastic scaling |
| Breach containment | Limited segmentation effectiveness | Micro-segmentation by default |
Adoption momentum confirms this architectural evolution. Data shows 96% of organizations have planned or implemented Zero Trust strategies integrating VPNs with identity-aware controls, recognizing that perimeter-based security no longer matches distributed workforce realities.
Cloud-native VPN platforms accelerate this transformation by eliminating on-premises infrastructure dependencies. These solutions deliver several advantages:
- Faster deployment without hardware procurement, data center space, or capacity planning delays.
- Simplified management through centralized cloud consoles replacing distributed gateway administration.
- Automatic scaling matching demand fluctuations without manual intervention or overprovisioning.
- Native integration with cloud identity providers and security services streamlining policy enforcement.
Market dynamics reflect this shift, with cloud-native VPNs holding 75% market revenue share as enterprises align secure access strategies with broader cloud migration initiatives. The operational simplicity and cost predictability of cloud platforms reduce friction preventing modernization.
Network security enterprises 2026 emphasizes integration between connectivity and security controls. Modern architectures unify secure access with threat detection, data loss prevention, and compliance monitoring in cohesive platforms. This convergence eliminates gaps between point solutions while providing holistic visibility into access patterns and risk indicators.
Organizations exploring why cloud based SD-WAN complements Zero Trust strategies discover synergies between optimized connectivity and granular access controls. Combining intelligent routing with identity-aware policies delivers both performance and security improvements over legacy approaches.
Pro Tip: Plan Zero Trust adoption in phases starting with high-risk applications or user groups, gathering feedback to refine policies before broad deployment, minimizing disruption while maximizing security gains.
Cloud networking SMB connectivity security 2026 demonstrates how even mid-sized organizations implement enterprise-grade secure access using cloud platforms previously accessible only to large enterprises. Democratization of advanced security capabilities levels the competitive playing field for businesses facing sophisticated threats regardless of size.
Framework for selecting and transitioning VPN solutions in business
IT leaders need structured approaches for evaluating secure access options and planning migrations minimizing operational disruption. This framework guides decision-making through five critical phases:
- Assess current VPN infrastructure complexity, cataloging services, gateways, user populations, and application dependencies to understand the existing landscape.
- Analyze user feedback through surveys, support tickets, and usage analytics identifying pain points driving workarounds or productivity losses.
- Evaluate security risks by reviewing breach histories, vulnerability reports, and compliance gaps requiring remediation.
- Research modern alternatives comparing Zero Trust platforms, cloud VPN providers, and hybrid approaches against organizational requirements.
- Plan phased implementation starting with pilot groups, measuring outcomes, refining policies, then expanding systematically across the organization.
Selection criteria should balance multiple factors beyond initial cost:
- Security strength including encryption standards, authentication methods, and breach containment capabilities.
- User experience covering connection speed, authentication friction, and cross-device consistency.
- Scalability supporting growth in users, locations, and application demands without architecture redesign.
- Zero Trust compatibility enabling future integration with identity providers, endpoint security, and cloud services.
- Operational simplicity reducing management overhead, consolidating tools, and automating routine tasks.
Tradeoff analysis helps prioritize competing concerns. Maximizing security through aggressive controls may impact user experience requiring careful policy tuning. Rapid deployment timelines might limit customization necessitating compromise on specific requirements. Understanding these tradeoffs prevents unrealistic expectations derailing projects.
How to secure remote networks SMB guide 2026 provides detailed implementation guidance applicable across organization sizes. Best practices include comprehensive user training explaining security rationale behind new procedures, transparent communication about migration timelines and expected changes, and continuous monitoring of adoption metrics detecting issues early.
Successful transitions maintain business continuity through parallel operation periods where old and new systems coexist. This approach allows gradual user migration, provides fallback options if issues arise, and builds confidence through demonstrated stability before final cutover.
Why secure connectivity matters extends beyond preventing breaches to enabling business agility. Modern secure access architectures support rapid onboarding of partners, seamless mergers and acquisitions integration, and flexible work arrangements attracting top talent. Strategic VPN modernization delivers competitive advantages transcending pure security improvements.
Common misconceptions about VPN security and usage
Clarity around VPN capabilities prevents false confidence undermining security planning. Several persistent myths require correction.
Myth 1: VPNs provide complete breach protection. Reality demonstrates that authentication alone creates insufficient defense. The implicit trust model grants authenticated attackers broad access for lateral movement, data exfiltration, and privilege escalation. Encryption protects data in transit but offers no visibility into user behavior or anomaly detection once inside the perimeter.
Myth 2: VPN performance problems represent minor inconveniences. User dissatisfaction statistics tell a different story. When 83% of users report frustration with VPN connectivity, the impact extends beyond annoyance to dangerous workarounds. Employees who disable security controls to meet deadlines create unmonitored access paths attackers exploit. Dismissing experience issues as trivial ignores their direct contribution to breach risks.
Myth 3: VPN network segmentation effectively isolates threats. Confidence metrics reveal uncomfortable truths. Research shows VPN segmentation effectiveness rates only 4.1 out of 10 among IT leaders, reflecting limited breach prevention in practice.
“IT security professionals express low confidence in VPN segmentation, rating effectiveness at just 4.1 out of 10, indicating traditional isolation methods fail against modern attack techniques.”
These misconceptions persist because VPN technology worked adequately in earlier threat environments. Perimeter security sufficed when networks contained most resources and remote access represented occasional exceptions. Cloud migration, distributed workforces, and sophisticated adversaries invalidated these assumptions. Strategies effective a decade ago now create vulnerabilities masked by outdated mental models.
Understanding realistic VPN limitations enables appropriate risk assessment and investment prioritization. Organizations maintaining legacy architectures should implement compensating controls like enhanced monitoring, strict least privilege policies, and regular access reviews. These measures reduce exposure while planning longer-term modernization addressing fundamental architectural weaknesses.
Conclusion: balancing security, usability, and future-proofing business VPNs
VPNs remain foundational to enterprise security but require urgent modernization addressing inherent vulnerabilities and operational challenges. Traditional implicit trust models expose organizations to breach risks through credential theft, zero-day exploits, and lateral movement once attackers gain authenticated access.
Integrating Zero Trust principles with cloud-native platforms transforms secure access from perimeter defense to continuous verification. This evolution improves both security posture through granular controls and user experience via seamless application access. The statistics confirm momentum, with 96% of organizations pursuing Zero Trust strategies recognizing architecture shifts as strategic imperatives rather than optional upgrades.
Incremental adoption using structured frameworks balances transformation benefits against operational risks. Phased deployments starting with high-risk user groups or critical applications allow policy refinement before broad rollout. This approach builds organizational confidence, captures lessons learned, and maintains business continuity throughout transitions.
Regular monitoring of security metrics, user satisfaction, and operational efficiency ensures VPN infrastructure adapts to evolving threats and business requirements. Feedback loops detecting emerging issues enable proactive responses preventing minor problems from escalating into major incidents or productivity barriers.
IT leaders should evaluate current VPN architectures against modern alternatives, assessing whether existing solutions adequately protect against contemporary threats while supporting workforce expectations. Proactive planning positions organizations to capture security, operational, and competitive advantages from secure access modernization before reactive crisis responses force suboptimal decisions under pressure.
Explore Sabertooth Pro’s secure connectivity solutions
Modernizing your secure access infrastructure requires reliable, scalable connectivity supporting advanced security architectures. Sabertooth Pro delivers wireless internet provider solutions and IoT solutions designed for enterprises implementing Zero Trust frameworks and cloud-native VPN platforms.
Our connectivity products, including the 5G Bolt wireless device, provide the high-performance, secure network foundation your VPN modernization strategy demands. With expertise spanning next-generation firewalls, SOC-as-a-Service, and zero-trust frameworks, we understand the connectivity requirements supporting your security transformation. Discover how tailored wireless and IoT data plans enhance your network infrastructure, enabling seamless integration of modern secure access controls while maintaining the reliability your business operations require.
FAQ
What are the primary security risks of using traditional VPNs in business?
Traditional VPNs face significant threats from credential theft through phishing, zero-day vulnerabilities in VPN software, and misconfigurations expanding attack surfaces. Their implicit trust models grant broad network access after initial authentication, enabling lateral movement for attackers who compromise legitimate credentials.
How does Zero Trust Network Access improve upon traditional VPN security?
ZTNA enforces continuous identity verification and device posture checks throughout sessions rather than trusting users after initial authentication. This approach implements least privilege access per application, limiting lateral movement and improving segmentation compared to the broad network access traditional VPNs grant.
What operational issues do users commonly report with business VPNs?
Users frequently complain about slow connection speeds degrading application performance, frequent disconnections interrupting workflows, and cumbersome multi-step authentication processes. These frustrations drive 83% user dissatisfaction rates and prompt risky workarounds like disabling VPNs or sharing credentials that undermine security.
What are best practices for transitioning from traditional VPNs to modern secure access solutions?
Start by assessing current VPN complexity and security risks through infrastructure audits and user feedback analysis. Plan phased deployments beginning with pilot groups, provide comprehensive training explaining new security procedures, and monitor adoption metrics continuously. Use frameworks balancing security requirements, user experience expectations, and operational capabilities to guide decisions and minimize disruption during migration.
